hdygxsj opened a new pull request, #13164: URL: https://github.com/apache/dolphinscheduler/pull/13164
<!--Thanks very much for contributing to Apache DolphinScheduler. Please review https://dolphinscheduler.apache.org/en-us/community/development/pull-request.html before opening a pull request.--> ## Purpose of the pull request close issue #12931 Currently, the dolphinscheduler can be attacked by a CSRF in the following ways. 1. First, someone exits the Dolphinscheduler site but does not clear the cookie 2. The dolphinscheduler api can then be accessed via cookies by other sites or others to submit forms or obtain information without authorization. For example: 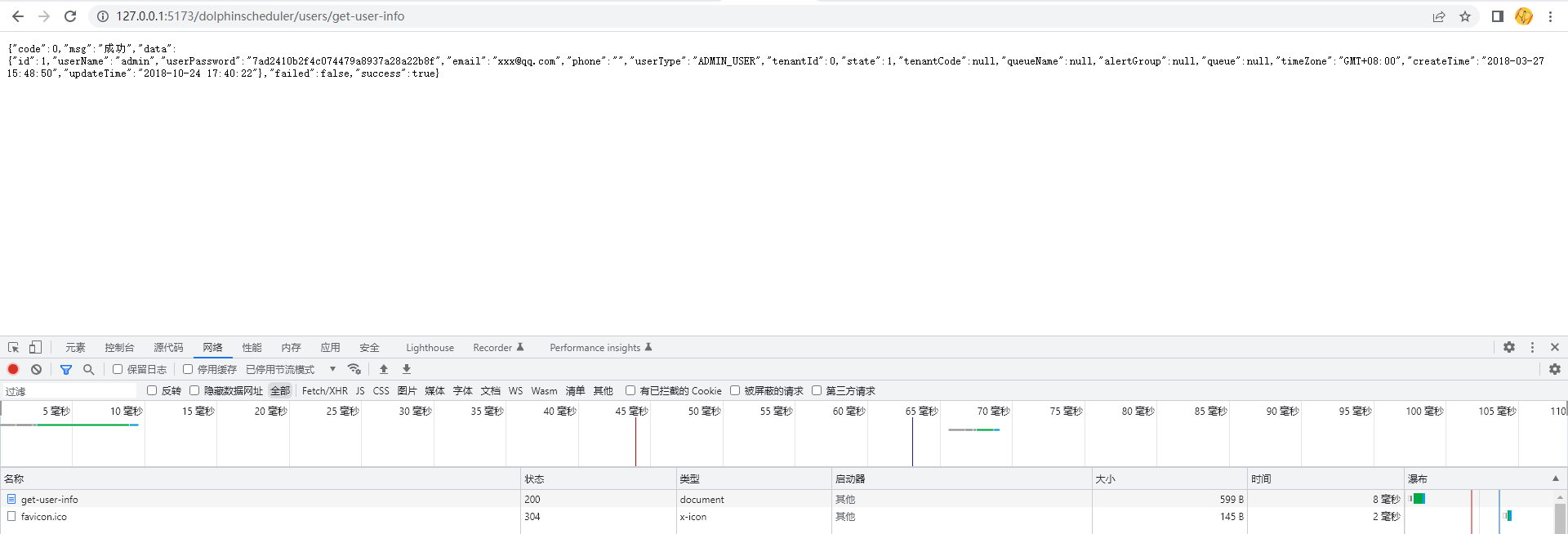 or ```html <form action="http://127.0.0.1:5173/dolphinscheduler/users/get-user-info"; method="get"> <input type="submit" value="提交" /> </form> ``` 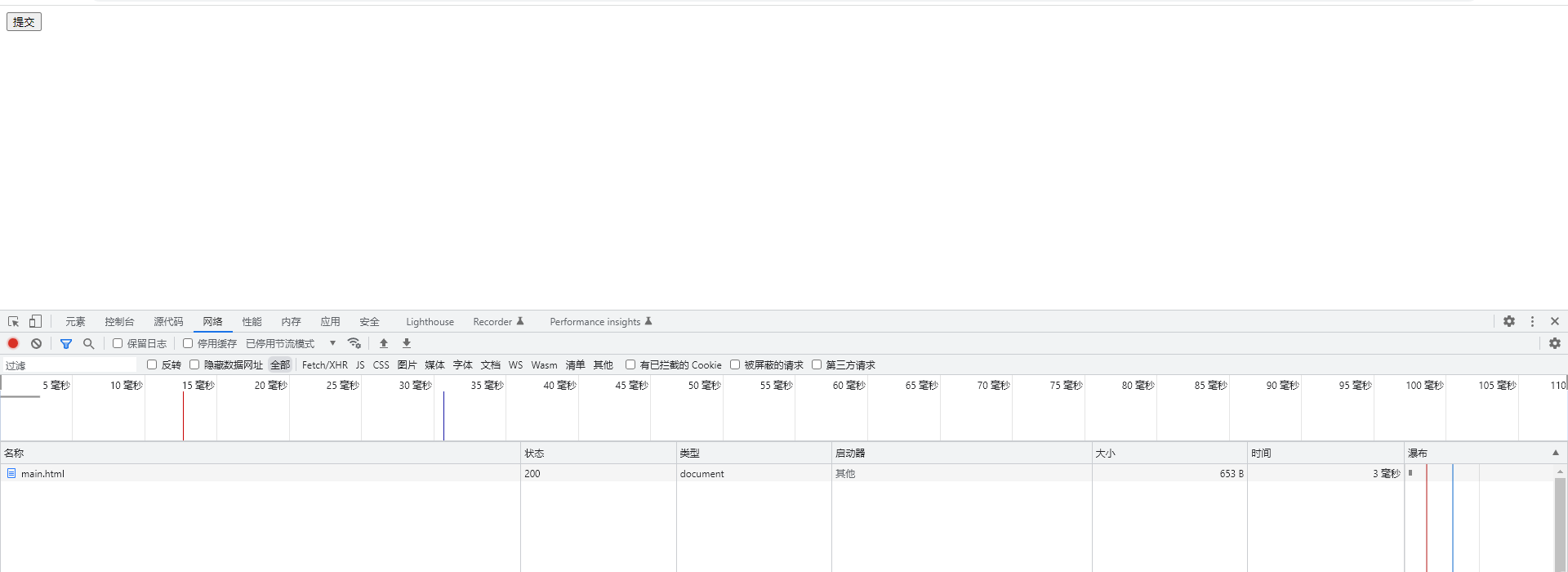 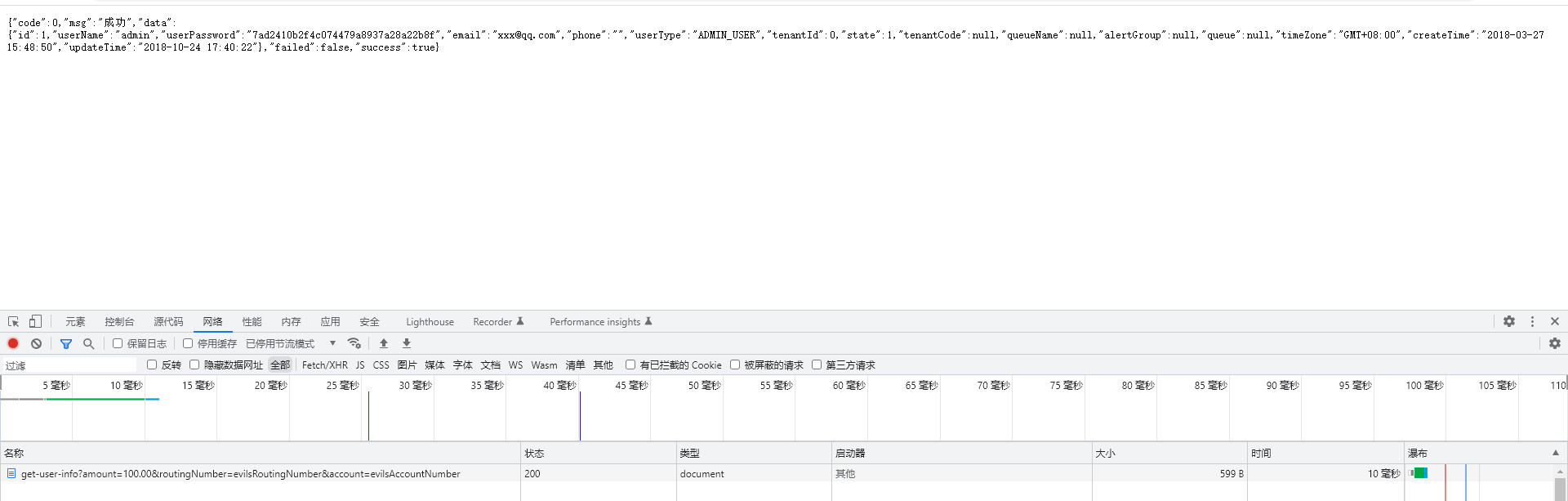 after this pr, when an attacker performs a CSRF attack, he will get a 403 exception. 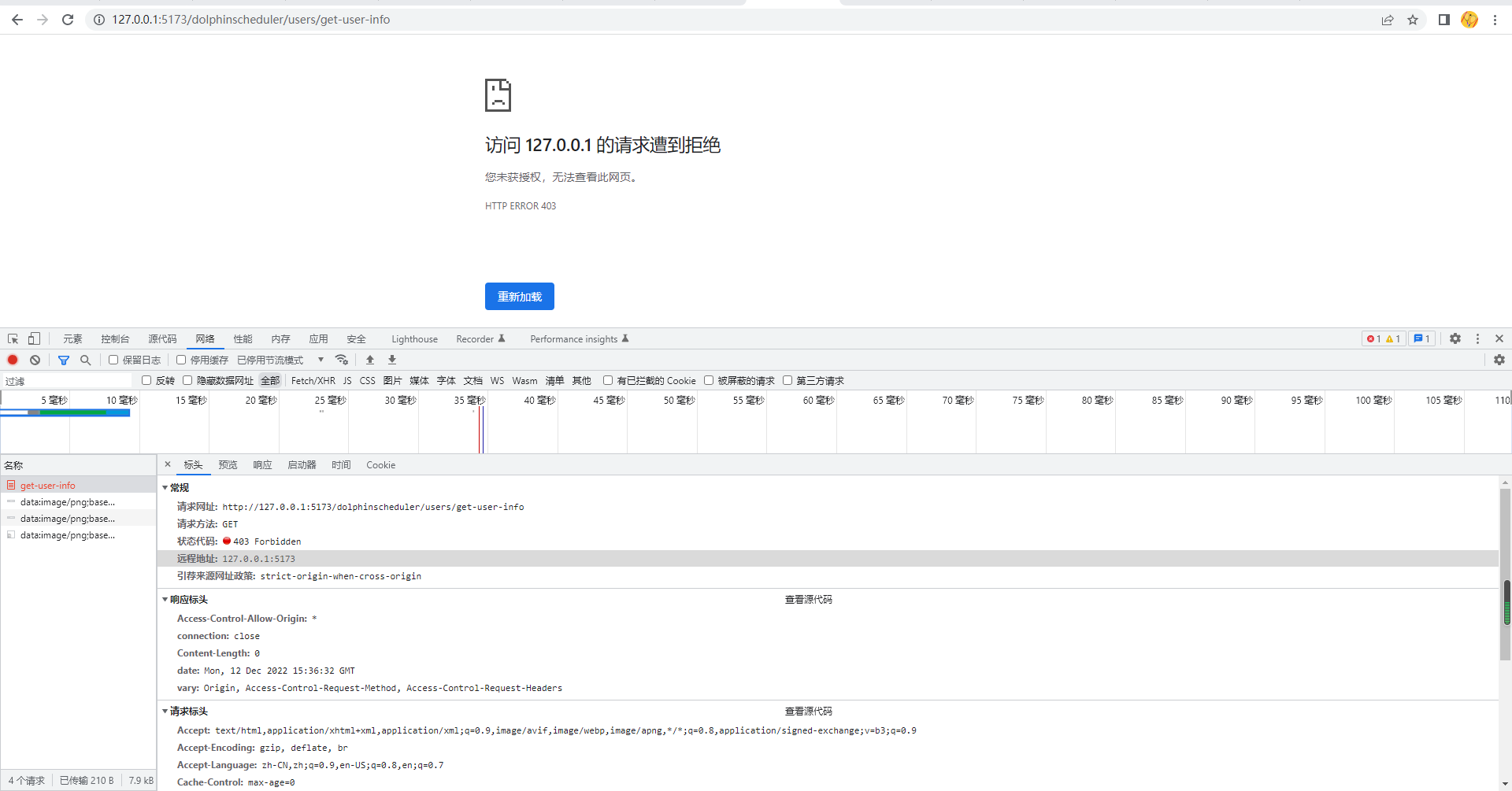 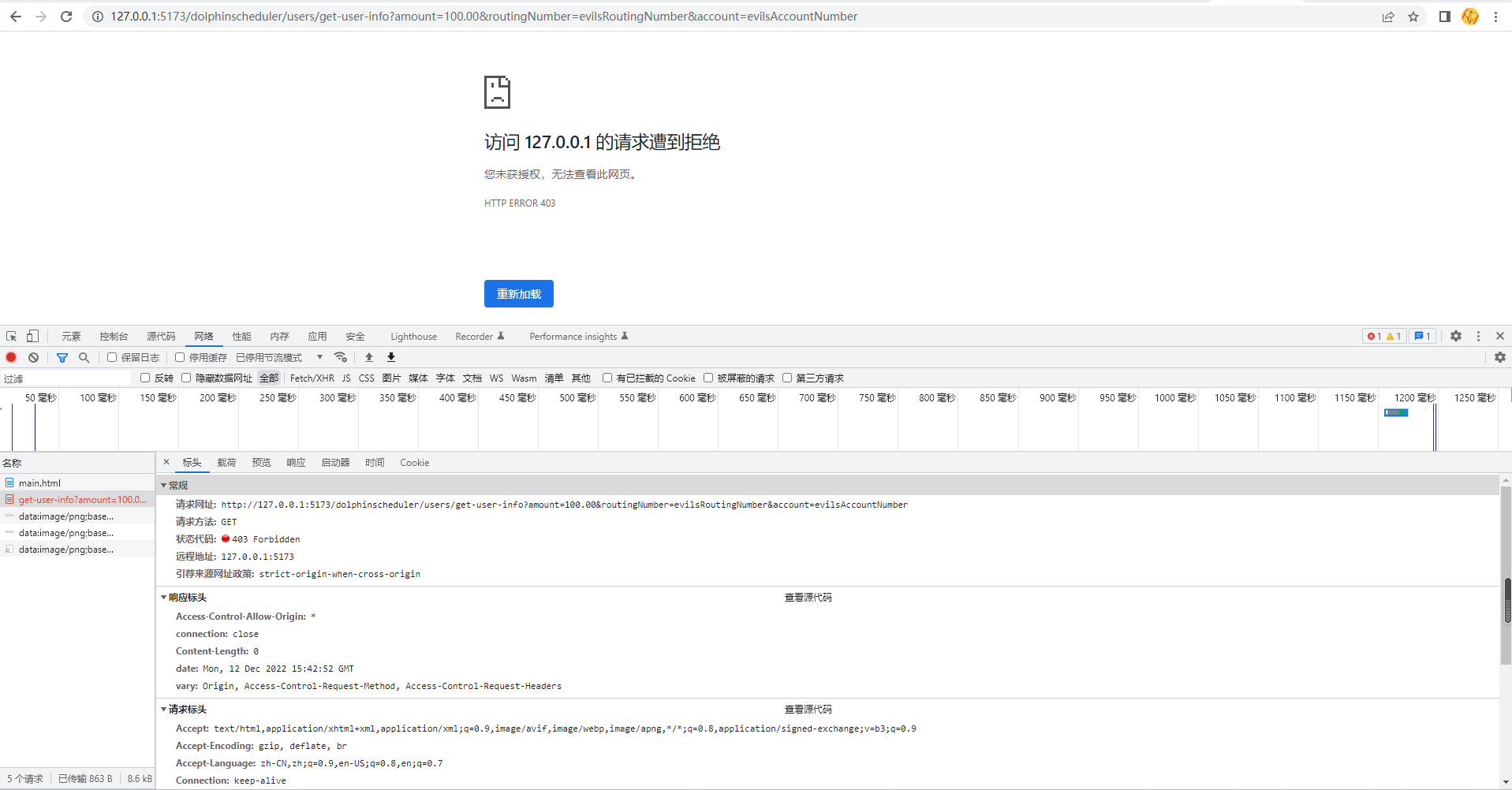 ## Brief change log I thought it would take a lot of work to introduce Spring security dependencies, so I added a CsrfTokenInterceptor to implement csrf defense. The CsrfTokenInterceptor does not intercept requests with the token in the http request header to ensure that the api is accessible through the token. The CsrfTokenInterceptor will get the X-CSRF-TOKEN from the http request header or the _csrf from the request paramter and verify their accuracy. And changed the ui module to add the request header X-CSRF-TOKEN when making an http request In the above way, dolphinscheduler can be protected from CSRF attacks only by ensuring that the attacker cannot obtain a correct csrf token ## Verify this pull request <!--*(Please pick either of the following options)*--> This pull request is code cleanup without any test coverage. *(or)* This pull request is already covered by existing tests, such as *(please describe tests)*. (or) This change added tests and can be verified as follows: <!--*(example:)* - *Added dolphinscheduler-dao tests for end-to-end.* - *Added CronUtilsTest to verify the change.* - *Manually verified the change by testing locally.* --> (or) If your pull request contain incompatible change, you should also add it to `docs/docs/en/guide/upgrede/incompatible.md` -- This is an automated message from the Apache Git Service. To respond to the message, please log on to GitHub and use the URL above to go to the specific comment. To unsubscribe, e-mail: [email protected] For queries about this service, please contact Infrastructure at: [email protected]
