Thelin90 opened a new issue #11405: URL: https://github.com/apache/druid/issues/11405
### Motivation Currently when pushing a cachedNamespace lookup, the password for the **JDBC** source is exposed, in plaintext in the lookups Apache Druid UI. 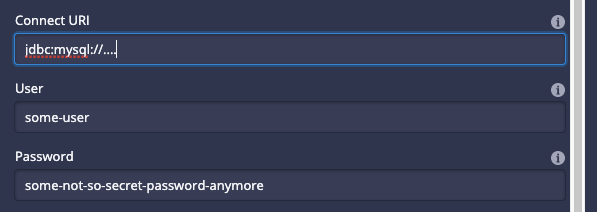 Would like it to look like this instead: 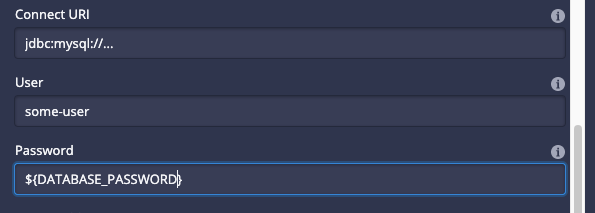 ### Proposed changes I would like to be able to mask this value, how? I am not sure, if it was possible to add an `env` into the `JSON` like: ```json { "type": "cachedNamespace", "extractionNamespace": { "type": "jdbc", "connectorConfig": { "connectURI": "jdbc:mysql://dburl:port/db?useSSL=false", "user": "some-user", "password": "${DATABASE_PASSWORD}", "createTables": false }, "table": "some-table", "keyColumn": "some-key-column", "tsColumn": "some-ts-column", "valueColumn": "some-value-column", "namespace": "default" }, "firstCacheTimeout": 12345678, "injective": true } ``` ### Rationale This would be simple since, then while deploying druid, you simply attach this `env` which can be fetched in a secure way. For instance with `k8s` within a `STS` or `deployment` file:: ```yaml - name: DATABASE_PASSWORD valueFrom: secretKeyRef: key: password name: db-secret ``` ### Operational impact Make passwords more protected. -- This is an automated message from the Apache Git Service. To respond to the message, please log on to GitHub and use the URL above to go to the specific comment. To unsubscribe, e-mail: [email protected] For queries about this service, please contact Infrastructure at: [email protected] --------------------------------------------------------------------- To unsubscribe, e-mail: [email protected] For additional commands, e-mail: [email protected]
