dlsprague commented on issue #8884: URL: https://github.com/apache/pulsar/issues/8884#issuecomment-755617182
thank you. Update to the issue: It is now successful using a different dependency which is bouncy castle and the connection is working with encryption enabled. However, there are black duck security vulnerabilities being reported. Using 2.6.2 client Bouncy castle jar file, an inner jar of pulsar client has some internal transitive dependencies with 1.6.0 version of bouncy castle which is causing the HIGH vulnerabilities. Using 2.7.0 High vulnerability is removed but it has 1 CRITICAL vulnerability with the new transitive dependency jar (bcprov-ext-jdk15on-1.66.jar 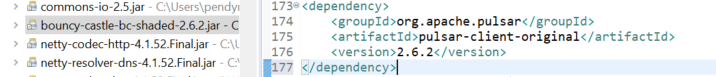 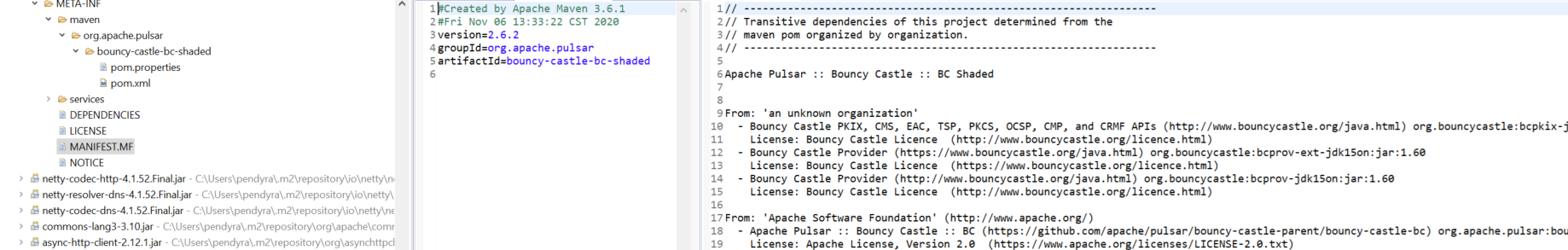 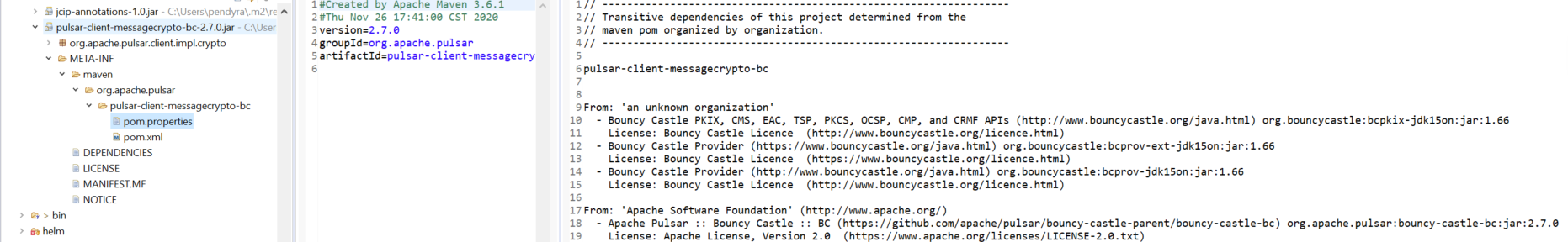 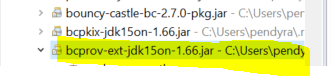 What can we do to resolve this vulverability? Thanks again. ---------------------------------------------------------------- This is an automated message from the Apache Git Service. To respond to the message, please log on to GitHub and use the URL above to go to the specific comment. For queries about this service, please contact Infrastructure at: [email protected]
