This is an automated email from the ASF dual-hosted git repository. mabin pushed a commit to branch houserush-sample in repository https://gitbox.apache.org/repos/asf/servicecomb-samples.git
commit 61f132fa99e9ef8081b1b865feb88f7438c709ed Author: linzb0123 <[email protected]> AuthorDate: Thu Aug 8 09:17:30 2019 +0800 fix the problems what the @MabinGo mentioned --- houserush/doc/images/ApiGateway.png | Bin 0 -> 27147 bytes houserush/gateway/README.md | 10 +++---- .../houserush/gateway/filter/AuthorizeFilter.java | 15 ++++------ houserush/login/pom.xml | 1 + .../practise/houserush/login/aggregate/User.java | 1 + .../houserush/login/service/UserServiceImpl.java | 17 ++++++++--- .../houserush/login/service/UserServiceTest.java | 31 +++++++++++++-------- 7 files changed, 44 insertions(+), 31 deletions(-) diff --git a/houserush/doc/images/ApiGateway.png b/houserush/doc/images/ApiGateway.png new file mode 100755 index 0000000..9db08d1 Binary files /dev/null and b/houserush/doc/images/ApiGateway.png differ diff --git a/houserush/gateway/README.md b/houserush/gateway/README.md index 3756401..66c595f 100755 --- a/houserush/gateway/README.md +++ b/houserush/gateway/README.md @@ -1,18 +1,17 @@ ## 微服务 gateway -该为微服务为API网关,作为对外的唯一入口,主要负责路由转发和鉴权。 +HouseRush应用网关,作为前端与后端通信的统一入口,为房源管理、订单中心等微服务提供路由和认证鉴权的功能 ### 主要功能 - API入口 - 动态路由 - 鉴权 -- 。。。 ### 设计原理 - 使用[zuul](https://github.com/Netflix/zuul/wiki)来设计实现API网关功能 - -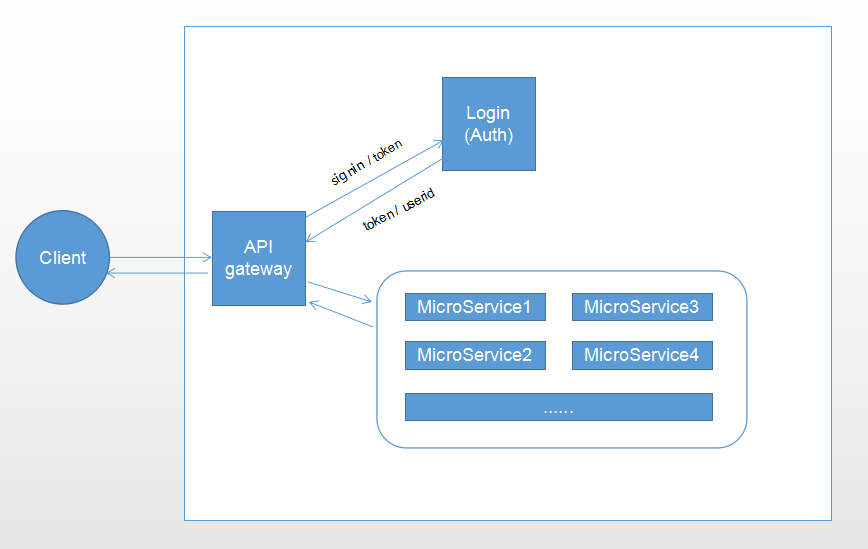 +- [使用zuul做边缘服务](https://docs.servicecomb.io/java-chassis/zh_CN/edge/zuul.html) + ### 实现 @@ -49,5 +48,4 @@ } - ``` - [使用zuul做边缘服务](https://docs.servicecomb.io/java-chassis/zh_CN/edge/zuul.html) \ No newline at end of file + ``` \ No newline at end of file diff --git a/houserush/gateway/src/main/java/org/apache/servicecomb/samples/practise/houserush/gateway/filter/AuthorizeFilter.java b/houserush/gateway/src/main/java/org/apache/servicecomb/samples/practise/houserush/gateway/filter/AuthorizeFilter.java index 390051e..f2230e2 100755 --- a/houserush/gateway/src/main/java/org/apache/servicecomb/samples/practise/houserush/gateway/filter/AuthorizeFilter.java +++ b/houserush/gateway/src/main/java/org/apache/servicecomb/samples/practise/houserush/gateway/filter/AuthorizeFilter.java @@ -21,6 +21,7 @@ import com.fasterxml.jackson.databind.ObjectMapper; import com.netflix.zuul.ZuulFilter; import com.netflix.zuul.context.RequestContext; import org.apache.commons.lang.StringUtils; +import org.apache.http.HttpStatus; import org.apache.servicecomb.provider.pojo.RpcReference; import org.apache.servicecomb.samples.practise.houserush.gateway.config.LoginUrlConfig; import org.apache.servicecomb.samples.practise.houserush.gateway.rpc.UserApi; @@ -36,8 +37,6 @@ import java.io.IOException; @Component public class AuthorizeFilter extends ZuulFilter { - private static final String SECRET = "231sdfqwer21313123cafkhioerutieweirqwuqbjffbqwrwr3"; - private static LoginUrlConfig loginUrlConfig = new LoginUrlConfig(); private static Logger log = LoggerFactory.getLogger(AuthorizeFilter.class); @@ -81,28 +80,26 @@ public class AuthorizeFilter extends ZuulFilter { return null; } } - sendResponse(403, "need login!"); + sendResponse(HttpStatus.SC_FORBIDDEN, "need login!"); } else if (loginUrlConfig.nologinUrlsSet.contains(key)) { if ("/login/signin".equals(requestUri)) { try { ObjectMapper mapper = new ObjectMapper(); User user = mapper.readValue(request.getInputStream(), User.class); - String username = user.getUsername(); - String password = user.getPassword(); User resultUser = userApi.signin(user); if (resultUser != null && resultUser.getToken() != null) { - sendResponse(200, "{\"token\": \"" + resultUser.getToken() + "\"}"); + sendResponse(HttpStatus.SC_OK, "{\"token\": \"" + resultUser.getToken() + "\"}"); } else { - sendResponse(401, "cannot sign in!"); + sendResponse(HttpStatus.SC_UNAUTHORIZED, "cannot sign in!"); } } catch (IOException e) { e.printStackTrace(); - sendResponse(401, e.getMessage()); + sendResponse(HttpStatus.SC_UNAUTHORIZED, e.getMessage()); } } return null; } else { - sendResponse(401, "the request url is not validate"); + sendResponse(HttpStatus.SC_UNAUTHORIZED, "the request url is not validate"); } return null; diff --git a/houserush/login/pom.xml b/houserush/login/pom.xml index 37eead4..3416bb3 100644 --- a/houserush/login/pom.xml +++ b/houserush/login/pom.xml @@ -69,6 +69,7 @@ <dependency> <groupId>org.springframework.boot</groupId> <artifactId>spring-boot-starter-test</artifactId> + <scope>test</scope> </dependency> </dependencies> diff --git a/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/aggregate/User.java b/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/aggregate/User.java index c36db7c..8b2793b 100755 --- a/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/aggregate/User.java +++ b/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/aggregate/User.java @@ -45,6 +45,7 @@ import java.util.Date; @Where(clause = "deleted_at is null") @EntityListeners(AuditingEntityListener.class) public class User { + // this is secret key,you can changed it to what you want private final static String USER_SECRET = "231sdfqwer21313123cafkhioerutieweirqwuqbjffbqwrwr3"; private final static String HASH_TYPE = "HmacSHA256"; @Id diff --git a/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceImpl.java b/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceImpl.java index 409fe94..79c0fb2 100755 --- a/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceImpl.java +++ b/houserush/login/src/main/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceImpl.java @@ -17,6 +17,8 @@ package org.apache.servicecomb.samples.practise.houserush.login.service; +import com.auth0.jwt.exceptions.TokenExpiredException; +import org.apache.http.HttpStatus; import org.apache.servicecomb.samples.practise.houserush.login.aggregate.User; import org.apache.servicecomb.samples.practise.houserush.login.dao.UserDao; import org.apache.servicecomb.swagger.invocation.exception.InvocationException; @@ -32,7 +34,7 @@ public class UserServiceImpl implements UserService { public User createUser(User user) { if (userDao.findByUsername(user.getUsername()) != null) { - throw new InvocationException(400, "", "用户名已存在"); + throw new InvocationException(HttpStatus.SC_BAD_REQUEST, "", "user already exists"); } String hashedPassword = user.makeHashedPassword(user.getPassword()); user.setHashedPassword(hashedPassword); @@ -71,7 +73,14 @@ public class UserServiceImpl implements UserService { } public User verifyToken(String token) { - int userId = User.verifyTokenGetUserId(token); + int userId; + try { + userId = User.verifyTokenGetUserId(token); + } catch (TokenExpiredException e) { + throw new InvocationException(HttpStatus.SC_BAD_REQUEST, "", "token has expired"); + } catch (Exception e) { + throw new InvocationException(HttpStatus.SC_BAD_REQUEST, "", "decode token fail"); + } User user = userDao.findOne(userId); user.generateToken(); return user; @@ -81,10 +90,10 @@ public class UserServiceImpl implements UserService { public boolean updatePassword(int id, String oldPassword, String newPassword) { User user = userDao.findOne(id); if (user == null) { - throw new InvocationException(400, "", "user not existed"); + throw new InvocationException(HttpStatus.SC_BAD_REQUEST, "", "user not existed"); } if (!user.getHashedPassword().equals(user.makeHashedPassword(oldPassword))) { - throw new InvocationException(400, "", "The password is incorrect"); + throw new InvocationException(HttpStatus.SC_BAD_REQUEST, "", "The password is incorrect"); } user.setHashedPassword(user.makeHashedPassword(newPassword)); userDao.save(user); diff --git a/houserush/login/src/test/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceTest.java b/houserush/login/src/test/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceTest.java index 71df9d2..8703ae7 100644 --- a/houserush/login/src/test/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceTest.java +++ b/houserush/login/src/test/java/org/apache/servicecomb/samples/practise/houserush/login/service/UserServiceTest.java @@ -68,9 +68,9 @@ public class UserServiceTest { newUser2.setPassword("123456"); try { userService.createUser(newUser2); - assert false; + fail("expect to occur an InvocationException but not"); } catch (InvocationException e) { - assert true; + assertEquals("InvocationException: code=400;msg=user already exists", e.getMessage()); } } @@ -86,16 +86,16 @@ public class UserServiceTest { //user not existed try { userService.updatePassword(10, "123456", "123456789"); - assert true; - } catch (Exception e) { - assert true; + fail("expect to occur an InvocationException but not"); + } catch (InvocationException e) { + assertEquals("InvocationException: code=400;msg=user not existed", e.getMessage()); } //password is incorrect try { userService.updatePassword(10, "12345", "123456789"); - assert true; - } catch (Exception e) { - assert true; + fail("expect to occur an InvocationException but not"); + } catch (InvocationException e) { + assertEquals("InvocationException: code=400;msg=The password is incorrect", e.getMessage()); } boolean success = userService.updatePassword(10, "123456", "123456789"); assertTrue(success); @@ -123,12 +123,19 @@ public class UserServiceTest { String token = user.getToken(); user = userService.verifyToken(token); assertThat(user.getId(), is(10)); - //verify fail + //token expired + try { + user = userService.verifyToken("eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJzdWIiOiI3NSIsImV4cCI6MTU2NTE2MzU4MH0.y1vz0mus91c9fje6GHzyzWQxlUA3h8eCg7za_kiATdg"); + fail("expect to occur an InvocationException but not"); + } catch (Exception e) { + assertEquals("InvocationException: code=400;msg=token has expired", e.getMessage()); + } + //invalid token expired try { - user = userService.verifyToken("incorrect token"); - assert false; + user = userService.verifyToken("invalid token"); + fail("expect to occur an InvocationException but not"); } catch (Exception e) { - assert true; + assertEquals("InvocationException: code=400;msg=decode token fail", e.getMessage()); } //login fail password incorrect User user2 = new User();
