slfan1989 commented on code in PR #4929:
URL: https://github.com/apache/hadoop/pull/4929#discussion_r1002292309
##########
hadoop-yarn-project/hadoop-yarn/hadoop-yarn-server/hadoop-yarn-server-resourcemanager/src/main/java/org/apache/hadoop/yarn/server/resourcemanager/webapp/dao/RMQueueAclInfo.java:
##########
@@ -25,9 +25,10 @@
@XmlRootElement
@XmlAccessorType(XmlAccessType.FIELD)
public class RMQueueAclInfo {
- protected boolean allowed;
- protected String user;
- protected String diagnostics;
+ private Boolean allowed;
Review Comment:
Thank you very much for helping to review the code.
If this field is `Boolean`, it is compatible with the original interface and
can achieve accurate information in Federation mode.
In Federation mode, we may have multiple SubClusters, and to verify whether
the user has queue permissions, multiple results may be returned, and these
results cannot be directly integrated.
For example, we have 2 SubClusters (SC-1, SC-2), user jack wants to have
access to the Default queue.
Due to configuration reasons, jack has the `default` queue permission of
`SC-1`, but does not have the queue permission of `SC-2`. If we call the router
interface, we may get into difficulties. I don't know if jack has permission to
access the default queue of the cluster. We cannot integrate information, but
should return the SubCluster situation to the user separately, which is more
reasonable.
We define `FederationRMQueueAclInfo` extend `RMQueueAclInfo`, If we call the
router's interface, we find that the return result is as follows:
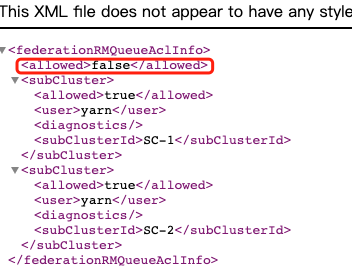
I tried to hide this field (allowed) and found that it cannot be hidden.
After reading the code, I found that if allowed is `Boolean` and the default
value is null, then this field can be hidden.
We access the router's interface again
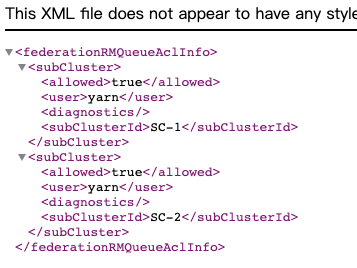
But does our setting `Boolean` affect the previous code?
We look at RM#RMWebServices#checkUserAccessToQueue, this method will set the
default value to ensure that the allowed field will be assigned and returned
RMWebServices#checkUserAccessToQueue
```
@GET
@Path(RMWSConsts.CHECK_USER_ACCESS_TO_QUEUE)
@Produces({ MediaType.APPLICATION_JSON + "; " + JettyUtils.UTF_8,
MediaType.APPLICATION_XML + "; " + JettyUtils.UTF_8 })
public RMQueueAclInfo checkUserAccessToQueue(
@PathParam(RMWSConsts.QUEUE) String queue,
@QueryParam(RMWSConsts.USER) String username,
@QueryParam(RMWSConsts.QUEUE_ACL_TYPE)
@DefaultValue("SUBMIT_APPLICATIONS") String queueAclType,
@Context HttpServletRequest hsr) throws AuthorizationException {
initForReadableEndpoints();
// For the user who invokes this REST call, he/she should have admin
access
// to the queue. Otherwise we will reject the call.
UserGroupInformation callerUGI = getCallerUserGroupInformation(hsr,
true);
if (callerUGI != null && !this.rm.getResourceScheduler().checkAccess(
callerUGI, QueueACL.ADMINISTER_QUEUE, queue)) {
throw new ForbiddenException(
"User=" + callerUGI.getUserName() + " doesn't haven access to
queue="
+ queue + " so it cannot check ACLs for other users.");
}
// Create UGI for the to-be-checked user.
UserGroupInformation user =
UserGroupInformation.createRemoteUser(username);
if (user == null) {
throw new ForbiddenException(
"Failed to retrieve UserGroupInformation for user=" + username);
}
// Check if the specified queue acl is valid.
QueueACL queueACL;
try {
queueACL = QueueACL.valueOf(queueAclType);
} catch (IllegalArgumentException e) {
throw new BadRequestException("Specified queueAclType=" + queueAclType
+ " is not a valid type, valid queue acl types={"
+ "SUBMIT_APPLICATIONS/ADMINISTER_QUEUE}");
}
if (!this.rm.getResourceScheduler().checkAccess(user, queueACL, queue)) {
return new RMQueueAclInfo(false, user.getUserName(),
"User=" + username + " doesn't have access to queue=" + queue
+ " with acl-type=" + queueAclType);
}
return new RMQueueAclInfo(true, user.getUserName(), "");
}
```
We changed to Boolean to fit the Federation mode well, and it has no effect
on the original code.
--
This is an automated message from the Apache Git Service.
To respond to the message, please log on to GitHub and use the
URL above to go to the specific comment.
To unsubscribe, e-mail: [email protected]
For queries about this service, please contact Infrastructure at:
[email protected]
---------------------------------------------------------------------
To unsubscribe, e-mail: [email protected]
For additional commands, e-mail: [email protected]
