thehackercat commented on code in PR #1945: URL: https://github.com/apache/dubbo-go/pull/1945#discussion_r963237838
########## xds/credentials/cert_manager.go: ########## @@ -0,0 +1,271 @@ +/* + * Licensed to the Apache Software Foundation (ASF) under one or more + * contributor license agreements. See the NOTICE file distributed with + * this work for additional information regarding copyright ownership. + * The ASF licenses this file to You under the Apache License, Version 2.0 + * (the "License"); you may not use this file except in compliance with + * the License. You may obtain a copy of the License at + * + * http://www.apache.org/licenses/LICENSE-2.0 + * + * Unless required by applicable law or agreed to in writing, software + * distributed under the License is distributed on an "AS IS" BASIS, + * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied. + * See the License for the specific language governing permissions and + * limitations under the License. + */ + +package credentials + +import ( + "bytes" + "context" + "crypto/tls" + "crypto/x509" + "encoding/pem" + "fmt" + "io/ioutil" + "os" + "strconv" + "strings" + "time" +) + +import ( + "github.com/dubbogo/gost/log/logger" +) + +import ( + "dubbo.apache.org/dubbo-go/v3/xds/client/bootstrap" + "dubbo.apache.org/dubbo-go/v3/xds/credentials/certgenerate" + "dubbo.apache.org/dubbo-go/v3/xds/credentials/certprovider" + "dubbo.apache.org/dubbo-go/v3/xds/credentials/certprovider/pemfile" + "dubbo.apache.org/dubbo-go/v3/xds/credentials/certprovider/remote" + "dubbo.apache.org/dubbo-go/v3/xds/internal" + "dubbo.apache.org/dubbo-go/v3/xds/utils/envconfig" +) + +func init() { + //init file_watcher builder + certprovider.Register(&pemfile.PluginBuilder{}) + //init builder func + internal.GetCertificateProviderBuilder = certprovider.GetBuilder +} + +//CertManager manage agent or no agent cert +type CertManager interface { + GetCertificate() ([]tls.Certificate, error) + GetRootCertificate() (*x509.CertPool, error) +} + +// NewCertManager return a manager +func NewCertManager() (CertManager, error) { + bootstrapPath := os.Getenv(envconfig.XDSBootstrapFileNameEnv) + if bootstrapPath != "" { + manager := &AgentCertManager{} + config, err := bootstrap.NewConfig() + if err != nil { + logger.Errorf("build bootstrap config error :%s", err.Error()) + return nil, err + } + certProvider, err := buildProvider(config.CertProviderConfigs, "default") + + if err != nil { + logger.Errorf("get cert provider error :%s", err.Error()) + return nil, err + } + manager.provider = certProvider + return manager, nil + } else { + manager := &CACertManager{} + manager.rootPath = RootCertPath + return manager, nil + } + +} + +// AgentCertManager work in istio agent mode +type AgentCertManager struct { + provider certprovider.Provider +} + +//GetRootCertificate return certificate of ca +func (c *AgentCertManager) GetRootCertificate() (*x509.CertPool, error) { + material, err := c.provider.KeyMaterial(context.Background()) + if err != nil { + return nil, err + } + return material.Roots, nil +} + +//GetCertificate return certificate of application +func (c *AgentCertManager) GetCertificate() ([]tls.Certificate, error) { + material, err := c.provider.KeyMaterial(context.Background()) + if err != nil { + return nil, err + } + return material.Certs, nil +} + +// buildProvider build cert provider from config +func buildProvider(configs map[string]*certprovider.BuildableConfig, instanceName string) (certprovider.Provider, error) { + cfg, ok := configs[instanceName] + if !ok { + return nil, fmt.Errorf("certificate provider instance %q not found in bootstrap file", instanceName) + } + provider, err := cfg.Build(certprovider.BuildOptions{ + CertName: "ca", + WantIdentity: true, + WantRoot: true, + }) + if err != nil { + return nil, fmt.Errorf("xds: failed to get security plugin instance (%+v): %v", cfg, err) + } + return provider, nil +} + +// CACertManager work in no agent mode, fetch cert form CA +type CACertManager struct { + // Certs contains a slice of cert/key pairs used to prove local identity. + Certs []tls.Certificate + // Roots contains the set of trusted roots to validate the peer's identity. + Roots *x509.CertPool + + NoAfter time.Time + + RootNoAfter time.Time + + rootPath string +} + +//GetCertificate return certificate of application +func (c *CACertManager) GetCertificate() ([]tls.Certificate, error) { + //cert expired + if time.Now().After(c.NoAfter) { + if err := c.UpdateCert(); err != nil { + return nil, err + } + } + return c.Certs, nil +} + +//GetRootCertificate return certificate of ca +func (c *CACertManager) GetRootCertificate() (*x509.CertPool, error) { + //root expired + if time.Now().After(c.RootNoAfter) { + if err := c.UpdateRoot(); err != nil { + return nil, err + } + } + return c.Roots, nil +} + +// UpdateRoot update root cert +func (c *CACertManager) UpdateRoot() error { + rootFileContents, err := ioutil.ReadFile(c.rootPath) + if err != nil { + return err + } + trustPool := x509.NewCertPool() + if !trustPool.AppendCertsFromPEM(rootFileContents) { + logger.Warn("failed to parse root certificate") + } + c.Roots = trustPool + block, _ := pem.Decode(rootFileContents) + if block == nil { + return fmt.Errorf("failed to decode certificate") + } + cert, err := x509.ParseCertificate(block.Bytes) + if err != nil { + return nil + } + c.RootNoAfter = cert.NotAfter + return nil +} + +// UpdateCert update cert +func (c *CACertManager) UpdateCert() error { + tokenProvider, err := NewSaTokenProvider(ServiceAccountPath) + if err != nil { + return err + } + + trustRoot, err := c.GetRootCertificate() + if err != nil { + return nil + } + citadelClient, err := remote.NewCitadelClient(&remote.Options{ + CAEndpoint: IstioCAEndpoint, + TrustedRoots: trustRoot, + TokenProvider: tokenProvider, + CertSigner: certSigner, + ClusterID: clusterID, + }) + if err != nil { + return err + } + host := "spiffe://" + "cluster.local" + "/ns/" + PodNamespace + "/sa/" + "default" Review Comment: 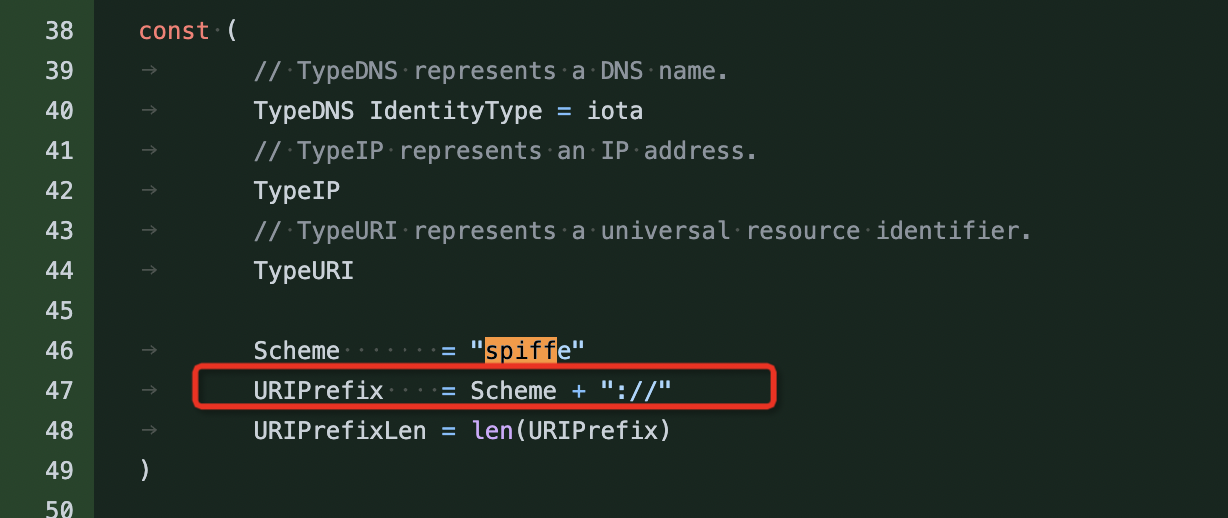 Could we make this host configurable, like this `URIPrifix`? -- This is an automated message from the Apache Git Service. To respond to the message, please log on to GitHub and use the URL above to go to the specific comment. To unsubscribe, e-mail: [email protected] For queries about this service, please contact Infrastructure at: [email protected] --------------------------------------------------------------------- To unsubscribe, e-mail: [email protected] For additional commands, e-mail: [email protected]
