[jira] [Created] (ZEPPELIN-4724) Zeppelin Documentation link in top menubar is broken for 0.9.0-SNAPSHOT
Krishna Pandey created ZEPPELIN-4724: Summary: Zeppelin Documentation link in top menubar is broken for 0.9.0-SNAPSHOT Key: ZEPPELIN-4724 URL: https://issues.apache.org/jira/browse/ZEPPELIN-4724 Project: Zeppelin Issue Type: Bug Components: documentation Affects Versions: 0.9.0 Reporter: Krishna Pandey Fix For: 0.9.0 The top menu bar for [http://zeppelin.apache.org/docs/0.9.0-SNAPSHOT/index.html] which consists of documentation related to "Quick Start", "Usage", "Setup", etc. has broken links. While the links displayed as part of the web page Table of Contents are updated with correct URLs e.g. for "HTTP Security Headers" it is http://zeppelin.apache.org/docs/0.9.0-SNAPSHOT/setup/security/http_security_headers.html, but drop-down menu link shows http://zeppelin.apache.org/setup/security/http_security_headers.html -- This message was sent by Atlassian Jira (v8.3.4#803005)
[jira] [Created] (ZEPPELIN-4723) Configure Security Features in Zeppelin to be enabled by default
Krishna Pandey created ZEPPELIN-4723: Summary: Configure Security Features in Zeppelin to be enabled by default Key: ZEPPELIN-4723 URL: https://issues.apache.org/jira/browse/ZEPPELIN-4723 Project: Zeppelin Issue Type: Improvement Components: zeppelin-web Affects Versions: 0.8.2 Reporter: Krishna Pandey Assignee: Krishna Pandey Fix For: 0.9.0 Zeppelin being a notebook has gained popularity among Data Scientists who are not necessarily also information security savvy. They usually deploy Zeppelin with default configuration options which doesn't enable the common web application security headers by default, e.g. zeppelin.server.xframe.options, zeppelin.server.strict.transport, zeppelin.server.xxss.protection, zeppelin.server.xcontent.type.options, zeppelin.server.xcontent.type.options documented [here|[https://zeppelin.apache.org/docs/0.8.2/setup/security/http_security_headers.html]]. This leaves the Zeppelin installation vulnerable. In recent times, Zeppelin installations are taking flak over these missing security headers from Internal Security teams and External Auditors who are not aware of these features being already available. Also, as software community is moving towards privacy-by-design and compliance-as-code, expectation of secure by design doesn't look out of the place. This Jira's intention is to enable all above HTTP response headers by default. -- This message was sent by Atlassian Jira (v8.3.4#803005)
[jira] [Created] (ZEPPELIN-4584) Default error page for Zeppelin masking Jetty Server version
Krishna Pandey created ZEPPELIN-4584: Summary: Default error page for Zeppelin masking Jetty Server version Key: ZEPPELIN-4584 URL: https://issues.apache.org/jira/browse/ZEPPELIN-4584 Project: Zeppelin Issue Type: Improvement Components: zeppelin-web Affects Versions: 0.8.2 Reporter: Krishna Pandey Assignee: Krishna Pandey Fix For: 0.8.3 When a non-existent notebook was accessed on the Browser, it shows the server name and version. As software development best practice, a generic error page should be displayed. -- This message was sent by Atlassian Jira (v8.3.4#803005)
Re: [ANNOUNCE] Apache Zeppelin 0.8.0 released
Awesome. Lots of new feature made it's way in this release. Kudos to all contributors. Thanks, Krishna Pandey On Thu, Jun 28, 2018 at 2:10 PM Chaoran Yu wrote: > Thanks Jeff for preparing the release. > > But the Docker image for 0.8.0 is failing: > https://hub.docker.com/r/apache/zeppelin/builds/ > > Can someone upload the new image to apache's docker hub account? > > Thank you, > Chaoran Yu > > > On 2018/06/28 03:06:46, Jeff Zhang wrote: > > The Apache Zeppelin community is pleased to announce the availability of> > > the 0.8.0 release.> > > > > Zeppelin is a collaborative data analytics and visualization tool for> > > distributed, general-purpose data processing system such as Apache > Spark,> > > Apache Flink, etc.> > > > > This is another major release after the last minor release 0.7.3.> > > The community put significant effort into improving Apache Zeppelin > since> > > the last release. 122 contributors fixed totally 602 issues. Lots of> > > new features are introduced, such as inline configuration, ipython> > > interpreter, yarn-cluster mode support , interpreter lifecycle manager> > > and etc.> > > > > We encourage you to download the latest release> > > fromhttp://zeppelin.apache.org/download.html> > > > > Release note is available> > > athttp://zeppelin.apache.org/releases/zeppelin-release-0.8.0.html> > > > > We welcome your help and feedback. For more information on the project > and> > > how to get involved, visit our website at http://zeppelin.apache.org/> > > > > Thank you all users and contributors who have helped to improve Apache> > > Zeppelin.> > > > > Regards,> > > The Apache Zeppelin community> > > >
[GitHub] zeppelin issue #2621: [Minor] Remove hardcoded key in zeppelinhub.
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2621 LGTM. It seems we are using SecureRandom which does not require seed explicitly to initialise and hence hardcoded key can be removed, unless we intentionally wanted a deterministic output. ---
[GitHub] zeppelin issue #2621: [Minor] Remove hardcoded key in zeppelinhub.
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2621 We need to consider below while removing the key. Are we relying on any such behaviour by specifying the seed value? "If two instances of Random are created with the same seed, and the same sequence of method calls is made for each, they will generate and return identical sequences of numbers." Refer: http://docs.oracle.com/javase/8/docs/api/java/util/Random.html ---
Re: [VOTE] Release Apache Zeppelin 0.7.3 (RC5)
+1 Ran PySpark and Spark use-cases successfully. Also verified PGP, SHA-512 and MD5 signatures for all binaries. Regards, Krishna Pandey On Mon, Sep 18, 2017 at 10:35 PM, Mina Lee wrote: > I propose the following RC to be released for the Apache Zeppelin 0.7.3 > release. > > The commit id is 5d246c96b054dcb8854e2beb924fc2c89b767fc1 which is > corresponds to the tag v0.7.3-rc5: > https://git-wip-us.apache.org/repos/asf?p=zeppelin.git;h= > refs/tags/v0.7.3-rc5 > > The release archives (tgz), signature, and checksums are here > https://dist.apache.org/repos/dist/dev/zeppelin/zeppelin-0.7.3-rc5/ > > The release candidate consists of the following source distribution archive > zeppelin-0.7.3.tgz > > In addition, the following supplementary binary distributions are provided > for user convenience at the same location > zeppelin-0.7.3-bin-all.tgz > zeppelin-0.7.3-bin-netinst.tgz > > The maven artifacts are here > https://repository.apache.org/content/repositories/orgapachezeppelin-1047 > > You can find the KEYS file here: > https://dist.apache.org/repos/dist/release/zeppelin/KEYS > > Release notes available at > https://issues.apache.org/jira/secure/ReleaseNote.jspa?versi > on=12341035&projectId=12316221 > > Vote will be open for next 72 hours (close at 10:30 21/Sep PDT). > > [ ] +1 approve > [ ] 0 no opinion > [ ] -1 disapprove (and reason why) >
Re: [VOTE] Release Apache Zeppelin 0.7.3 (RC3)
+1 Ran PySpark and Spark use-cases successfully. Also verified PGP, SHA-512 and MD5 signatures for all binaries. On Wed, Sep 13, 2017 at 6:52 PM, Mina Lee wrote: > I propose the following RC to be released for the Apache Zeppelin 0.7.3 > release. > > The commit id is 42c1810ef901eb8dba923385f3c305d7f7b11a70 which is > corresponds to the tag v0.7.3-rc3: > https://git-wip-us.apache.org/repos/asf?p=zeppelin.git;h= > refs/tags/v0.7.3-rc3 > > The release archives (tgz), signature, and checksums are here > https://dist.apache.org/repos/dist/dev/zeppelin/zeppelin-0.7.3-rc3/ > > The release candidate consists of the following source distribution archive > zeppelin-0.7.3.tgz > > In addition, the following supplementary binary distributions are provided > for user convenience at the same location > zeppelin-0.7.3-bin-all.tgz > zeppelin-0.7.3-bin-netinst.tgz > > The maven artifacts are here > https://repository.apache.org/content/repositories/orgapachezeppelin-1046 > > You can find the KEYS file here: > https://dist.apache.org/repos/dist/release/zeppelin/KEYS > > Release notes available at > https://issues.apache.org/jira/secure/ReleaseNote.jspa?versi > on=12341035&projectId=12316221 > > Vote will be open for next 72 hours (close at 06:30 16/Sep PDT). > > [ ] +1 approve > [ ] 0 no opinion > [ ] -1 disapprove (and reason why) >
[GitHub] zeppelin issue #2589: [DOC] 0.7.3 release note
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2589 LGTM except minor comment. ---
[GitHub] zeppelin issue #2564: [ZEPPELIN-2896] Replacing addHeader with setHeader met...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2564 @1ambda @Leemoonsoo Can you please help review this fix? As this is related to [ZEPPELIN-2775] which is getting shipped in 0.7.3, we may want to merge this now and get this as well into RC2. ---
[GitHub] zeppelin pull request #2564: [ZEPPELIN-2896] Replacing addHeader with setHea...
Github user krishna-pandey closed the pull request at: https://github.com/apache/zeppelin/pull/2564 ---
[GitHub] zeppelin pull request #2564: [ZEPPELIN-2896] Replacing addHeader with setHea...
GitHub user krishna-pandey reopened a pull request: https://github.com/apache/zeppelin/pull/2564 [ZEPPELIN-2896] Replacing addHeader with setHeader method in CorsFilter.java ### What is this PR for? HTTP Response Headers were being added multiple times. Replacing addHeader method with setHeader overrides the Response Header value with new/existing value instead of adding another duplicate response Header. ### What type of PR is it? [Bug Fix] ### What is the Jira issue? * https://issues.apache.org/jira/browse/ZEPPELIN-2896 ### How should this be tested? Open the Zeppelin URL in Chrome Browser. Select "More Tools" -> "Developer Tools" from the right-side menu. Under Network Section, select the request with name "localhost" and check for "Response Headers". You should see response headers appearing only once. 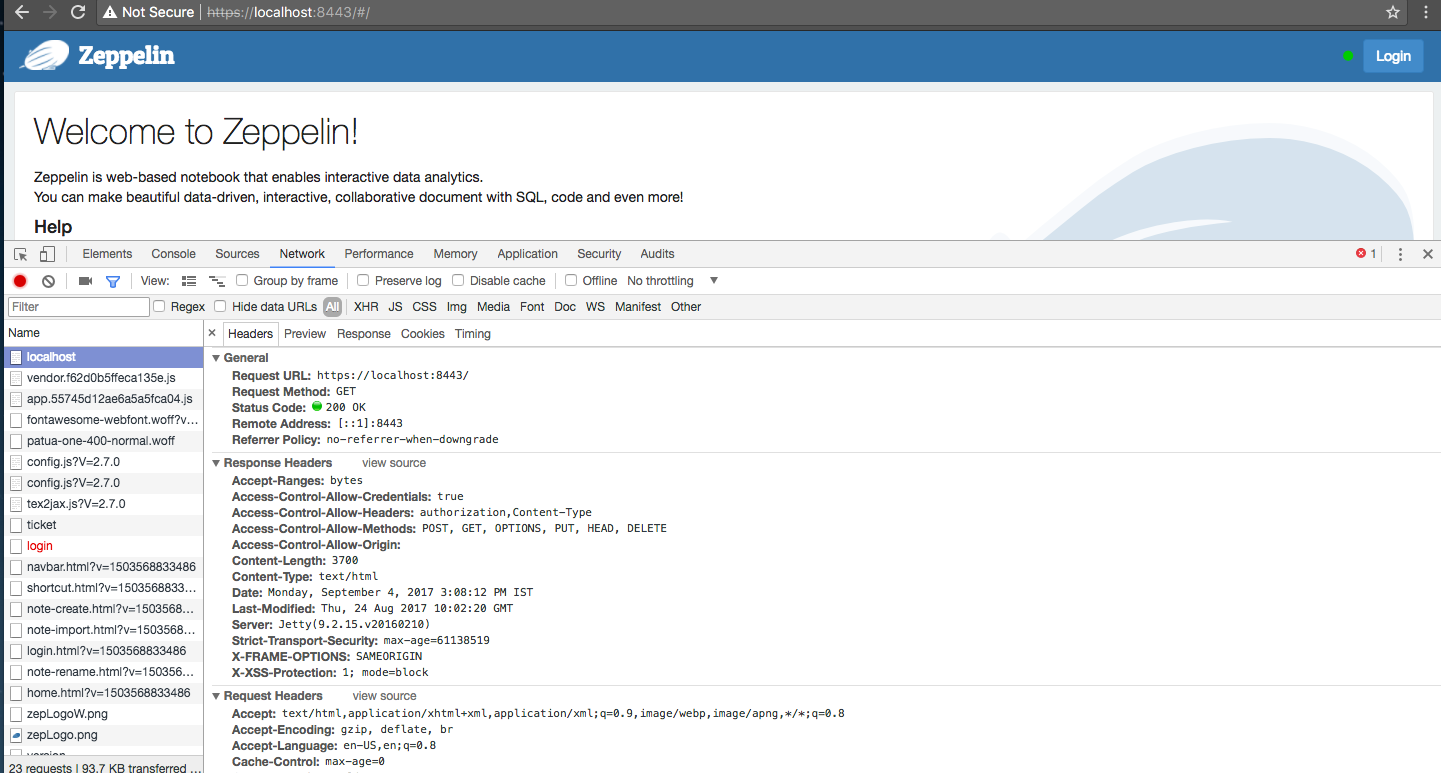 You can merge this pull request into a Git repository by running: $ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2896 Alternatively you can review and apply these changes as the patch at: https://github.com/apache/zeppelin/pull/2564.patch To close this pull request, make a commit to your master/trunk branch with (at least) the following in the commit message: This closes #2564 ---
[GitHub] zeppelin issue #2564: [ZEPPELIN-2896] Replacing addHeader with setHeader met...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2564 @felixcheung IMHO, it happens coz we first hit the root Context Path and Jetty redirecting it later to the landing/welcome page i.e. index.html. These headers are duplicated only for such requests and not every request. ---
[GitHub] zeppelin issue #2564: [ZEPPELIN-2896] Replacing addHeader with setHeader met...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2564 @1ambda, @Leemoonsoo, @felixcheung, @jongyoul, @prabhjyotsingh Please help review this. ---
[GitHub] zeppelin pull request #2564: [ZEPPELIN-2896] Replacing addHeader with setHea...
GitHub user krishna-pandey opened a pull request: https://github.com/apache/zeppelin/pull/2564 [ZEPPELIN-2896] Replacing addHeader with setHeader method in CorsFilter.java ### What is this PR for? HTTP Response Headers were being added multiple times. Replacing addHeader method with setHeader overrides the Response Header value with new/existing value instead of adding another duplicate response Header. ### What type of PR is it? [Bug Fix] ### What is the Jira issue? * https://issues.apache.org/jira/browse/ZEPPELIN-2896 ### How should this be tested? Open the Zeppelin URL in Chrome Browser. Select "More Tools" -> "Developer Tools" from the right-side menu. Under Network Section, select the request with name "localhost" and check for "Response Headers". You should see response headers appearing only once. 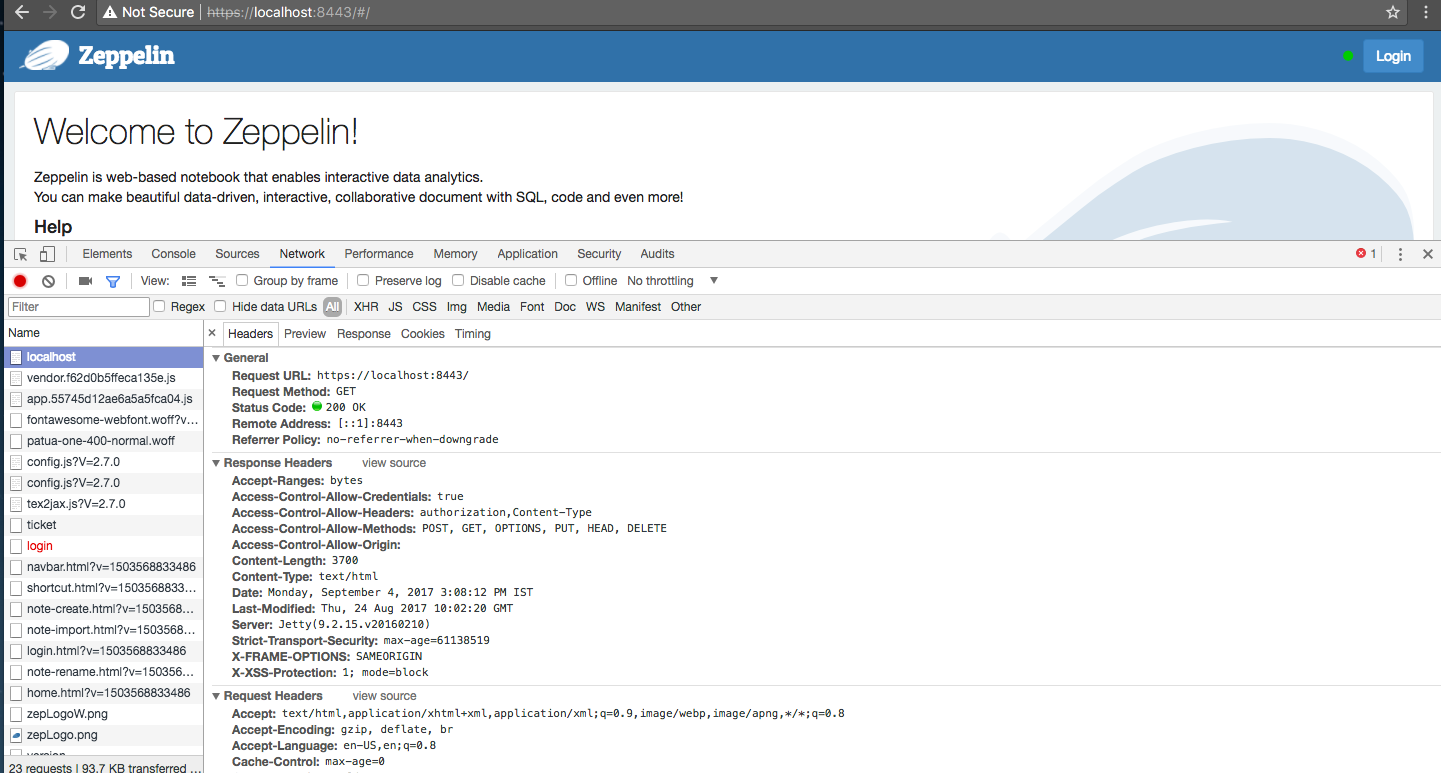 You can merge this pull request into a Git repository by running: $ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2896 Alternatively you can review and apply these changes as the patch at: https://github.com/apache/zeppelin/pull/2564.patch To close this pull request, make a commit to your master/trunk branch with (at least) the following in the commit message: This closes #2564 commit 89a3fdcd3994070f872ca755587a0f10f76c6917 Author: krishna-pandey Date: 2017-09-04T09:39:59Z replacing addHeader with setHeader ---
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 @1ambda I am able to reproduce the issue, seems like the value is getting repeated. It turns out that all Headers are being set multiple times. I have created an issue (ZEPPELIN-2896) for that. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[jira] [Created] (ZEPPELIN-2896) HTTP Response headers are being set multiple times
Krishna Pandey created ZEPPELIN-2896: Summary: HTTP Response headers are being set multiple times Key: ZEPPELIN-2896 URL: https://issues.apache.org/jira/browse/ZEPPELIN-2896 Project: Zeppelin Issue Type: Bug Components: zeppelin-server Affects Versions: 0.7.2 Reporter: Krishna Pandey Priority: Critical HTTP Response Headers are being set multiple times. Refer screenshot attached. -- This message was sent by Atlassian JIRA (v6.4.14#64029)
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 @1ambda What's the value you are providing for "zeppelin.server.xxss.protection" property. It can take three possible values "0", "1" or "1; mode=block". --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
Re: [DISCUSS] Release 0.7.3
+1 On Tue, Aug 29, 2017 at 12:28 PM, Prabhjyot Singh wrote: > Hi, > > Since 0.7.2 release, we have resolved 22 issues and that includes most of > the critical issues in 0.7.3 umbrella issue [1]. > > With these bugs fixes, it makes Zeppelin moves towards stability, and I'd > like to proceed release process for 0.7.3 at this point and provide stable > release. > > Remaining issue can be resolved in 0.8.0 release (or 0.7.4 if another > maintenance release is necessary). > > Shell we proceed to 0.7.3? > > Thanks and Regards, > Prabhjyot Singh > > [1] https://issues.apache.org/jira/browse/ZEPPELIN-2864 > > -- > > Warm Regards, > > Prabhjyot Singh >
[GitHub] zeppelin issue #2550: [MINOR] Updated shiro.ini.template to include secure c...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2550 LGTM! --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2550: [MINOR] Updated shiro.ini.template to include secure c...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2550 @VipinRathor Also, I think it will be a good idea to mention an one-liner in the shiro.ini.template "Enable 'cookie.secure = true' only when Zeppelin is running on HTTPS" or something similar. If enabled when Zeppelin is running on HTTP, Browser does not set the cookie and hence user session won't be maintained. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2550: [MINOR] Updated shiro.init.template to include secure ...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2550 @VipinRathor Can you please update the description from "Updated shiro.init.template ..." to "Updated shiro.ini.template ...". --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 @felixcheung Updated the documentation as per review. Let me know if any other changes are required. Thanks. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 @felixcheung Made the change as suggested. Also provided documentation for all HTTP Security Headers support we added recently (tested it locally). Let me know if I am still missing anything. Thanks for the review. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 Above commit also took care of below test case failures. https://s3.amazonaws.com/archive.travis-ci.org/jobs/253571796/log.txt?X-Amz-Expires=30&X-Amz-Date=20170717T114927Z&X-Amz-Algorithm=AWS4-HMAC-SHA256&X-Amz-Credential=AKIAJRYRXRSVGNKPKO5A/20170717/us-east-1/s3/aws4_request&X-Amz-SignedHeaders=host&X-Amz-Signature=c08313e7f165e576846f035b0dee0975d4fc5fb414a0fa291e759b1993dd9b7b --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2494: Broken link on Apache Zeppelin website
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2494 I have also logged this issue as [ZEPPELIN-2783](https://issues.apache.org/jira/browse/ZEPPELIN-2783) --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
Broken link on Apache Zeppelin website
Hi All, Whenever we raise a Pull Request for Apache Zeppelin, we are presented with a helping Questionnaire. One such question is below which points to Contribution guide. ### What is this PR for? A few sentences describing the overall goals of the pull request's commits. First time? Check out the contributing guide - https://zeppelin.apache.org/ contribution/contributions.html When you land on the webpage following the above link and click Community drop-down list on top menu and then click "Contributors" link, it throws a HTTP 404 error "The requested URL /contribution/community.html was not found on this server." Thanks, Krishna Pandey
[jira] [Created] (ZEPPELIN-2783) Broken link at Apache Zeppelin website's Contributions page
Krishna Pandey created ZEPPELIN-2783:
Summary: Broken link at Apache Zeppelin website's Contributions
page
Key: ZEPPELIN-2783
URL: https://issues.apache.org/jira/browse/ZEPPELIN-2783
Project: Zeppelin
Issue Type: Bug
Components: documentation, Homepage
Environment: Apache Zeppelin Website
(https://zeppelin.apache.org/contribution/contributions.html)
Reporter: Krishna Pandey
Priority: Critical
Whenever we raise a Pull Request for Apache Zeppelin, we are presented with a
helping Questionnaire. One such question is below which points to Contribution
guide.
{noformat}
### What is this PR for?
A few sentences describing the overall goals of the pull request's commits.
First time? Check out the contributing guide -
https://zeppelin.apache.org/contribution/contributions.html
{noformat}
When you land on the webpage following the above link and click Community
drop-down list on top menu and then click "Contributors" link, it throws error
"The requested URL /contribution/community.html was not found on this server."
--
This message was sent by Atlassian JIRA
(v6.4.14#64029)
[GitHub] zeppelin issue #2492: [ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Pr...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2492 @Leemoonsoo, @felixcheung, @jongyoul, @prabhjyotsingh Please help review this. Note: Chrome Browser seems to be ignoring "X-XSS-Protection" header when value is set to 1. Ideally, it should be set to "X-XSS-Protection:1; mode=block". Difference being when later value is set, the browser will prevent rendering of the page if an attack is detected rather than sanitizing the page as in previous case. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin pull request #2492: [ZEPPELIN-2775] Strict-Transport-Security and X...
GitHub user krishna-pandey opened a pull request:
https://github.com/apache/zeppelin/pull/2492
[ZEPPELIN-2775] Strict-Transport-Security and X-XSS-Protection Headers
### What is this PR for?
The HTTP Strict-Transport-Security response header (often abbreviated as
HSTS) is a security feature that lets a web site tell browsers that it should
only be communicated with using HTTPS, instead of using HTTP.
Note: The Strict-Transport-Security header is ignored by the browser when
your site is accessed using HTTP; this is because an attacker may intercept
HTTP connections and inject the header or remove it. When your site is accessed
over HTTPS with no certificate errors, the browser knows your site is HTTPS
capable and will honor the Strict-Transport-Security header.
The HTTP X-XSS-Protection response header is a feature of Internet
Explorer, Chrome and Safari that stops pages from loading when they detect
reflected cross-site scripting (XSS) attacks.
### What type of PR is it?
[Bug Fix | Improvement ]
### What is the Jira issue?
* [ZEPPELIN-2775](https://issues.apache.org/jira/browse/ZEPPELIN-2775)
### How should this be tested?
Make a curl call to Zeppelin? Go to Chrome Browser and select "More Tools"
-> "Developer Tools" from the right-side menu. Under Network Section, select
any request and check for "Response Headers". You should see below headers
along with existing ones.
> strict-transport-security:max-age=631138519
> x-xss-protection:1; mode=block
https://user-images.githubusercontent.com/6433184/28217231-16ce6cee-68d2-11e7-91aa-77ad083612c7.png";>
### Questions:
* Does this needs documentation?
You can merge this pull request into a Git repository by running:
$ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2775
Alternatively you can review and apply these changes as the patch at:
https://github.com/apache/zeppelin/pull/2492.patch
To close this pull request, make a commit to your master/trunk branch
with (at least) the following in the commit message:
This closes #2492
commit 468231cc6577b2acf8fbd592177fee9ad1b067b4
Author: krishna-pandey
Date: 2017-07-14T11:34:36Z
Added configurable Strict-Transport-Security and X-XSS-Protection Headers
---
If your project is set up for it, you can reply to this email and have your
reply appear on GitHub as well. If your project does not have this feature
enabled and wishes so, or if the feature is enabled but not working, please
contact infrastructure at infrastruct...@apache.org or file a JIRA ticket
with INFRA.
---
[jira] [Created] (ZEPPELIN-2775) Add configurable Strict-Transport-Security and X-XSS-Protection Headers
Krishna Pandey created ZEPPELIN-2775: Summary: Add configurable Strict-Transport-Security and X-XSS-Protection Headers Key: ZEPPELIN-2775 URL: https://issues.apache.org/jira/browse/ZEPPELIN-2775 Project: Zeppelin Issue Type: Bug Components: zeppelin-server Affects Versions: 0.7.2 Reporter: Krishna Pandey The *HTTP Strict-Transport-Security* response header (often abbreviated as HSTS) is a security feature that lets a web site tell browsers that it should only be communicated with using HTTPS, instead of using HTTP. *Note:* The Strict-Transport-Security header is ignored by the browser when your site is accessed using HTTP; this is because an attacker may intercept HTTP connections and inject the header or remove it. When your site is accessed over HTTPS with no certificate errors, the browser knows your site is HTTPS capable and will honor the Strict-Transport-Security header. *An example scenario* You log into a free WiFi access point at an airport and start surfing the web, visiting your online banking service to check your balance and pay a couple of bills. Unfortunately, the access point you're using is actually a hacker's laptop, and they're intercepting your original HTTP request and redirecting you to a clone of your bank's site instead of the real thing. Now your private data is exposed to the hacker. Strict Transport Security resolves this problem; as long as you've accessed your bank's web site once using HTTPS, and the bank's web site uses Strict Transport Security, your browser will know to automatically use only HTTPS, which prevents hackers from performing this sort of man-in-the-middle attack. *Syntax* Strict-Transport-Security: max-age= Strict-Transport-Security: max-age=; includeSubDomains Strict-Transport-Security: max-age=; preload Read more at https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Strict-Transport-Security The HTTP *X-XSS-Protection* response header is a feature of Internet Explorer, Chrome and Safari that stops pages from loading when they detect reflected cross-site scripting (XSS) attacks. *Syntax* X-XSS-Protection: 0 X-XSS-Protection: 1 X-XSS-Protection: 1; mode=block X-XSS-Protection: 1; report= Read more at https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/X-XSS-Protection -- This message was sent by Atlassian JIRA (v6.4.14#64029)
[GitHub] zeppelin issue #2482: [ZEPPELIN-2765] Configurable X-FRAME-OPTIONS for Zeppe...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2482 @felixcheung Thanks for the review. Fixed the value. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin issue #2482: [ZEPPELIN-2765] Configurable X-FRAME-OPTIONS for Zeppe...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2482 @Leemoonsoo, @felixcheung, @jongyoul, @prabhjyotsingh Please help review this. --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin pull request #2482: [ZEPPELIN-2765] Configurable X-FRAME-OPTIONS fo...
GitHub user krishna-pandey opened a pull request: https://github.com/apache/zeppelin/pull/2482 [ZEPPELIN-2765] Configurable X-FRAME-OPTIONS for Zeppelin ### What is this PR for? The X-Frame-Options HTTP response header can be used to indicate whether or not a browser should be allowed to render a page in a or . Sites can use this to avoid Clickjacking attacks, by ensuring that their content is not embedded into other sites. Set the X-Frame-Options header for all responses containing HTML content. The possible values are "DENY", "SAMEORIGIN", or "ALLOW-FROM uri" ### What type of PR is it? [Bug Fix | Improvement ] ### What is the Jira issue? * [ZEPPELIN-2765](https://issues.apache.org/jira/browse/ZEPPELIN-2765) ### How should this be tested? The application (Zeppelin) loads in iframe. Put below code in a html file and open in browser: You can merge this pull request into a Git repository by running: $ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2765 Alternatively you can review and apply these changes as the patch at: https://github.com/apache/zeppelin/pull/2482.patch To close this pull request, make a commit to your master/trunk branch with (at least) the following in the commit message: This closes #2482 commit 518f1a4a213614d038b4fd554614afe8ec2c8c20 Author: krishna-pandey Date: 2017-07-11T12:09:37Z Configurable X-FRAME-OPTIONS for Zeppelin --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[jira] [Created] (ZEPPELIN-2765) Configurable X-FRAME-OPTIONS for Zeppelin
Krishna Pandey created ZEPPELIN-2765: Summary: Configurable X-FRAME-OPTIONS for Zeppelin Key: ZEPPELIN-2765 URL: https://issues.apache.org/jira/browse/ZEPPELIN-2765 Project: Zeppelin Issue Type: Improvement Components: zeppelin-server Affects Versions: 0.7.0 Reporter: Krishna Pandey *Information systems must not be susceptible to Cross-frame Scripting (XFS) attacks and clickjacking.* Information systems must implement proper input validation and output encoding. With proper input validation and output encoding, information systems will not be susceptible to cross-frame scripting, either stored or reflected. A successful cross-frame scripting attack may redirect a user to a malicious third-party page. *Technical Risk* : Without proper input validation and output encoding, information systems are susceptible to cross-frame scripting, which may result in unauthorized access or malicious attacks against the user. *Corrective Action* : This issue can be fixed using the following methods1. Implementing the response header X-Frame- Options and set the value to 'Deny' or 'same origin'.2. Sending the proper browser response headers that instruct the browser to not allow framing from other domains . The application (Zeppelin) loads in iframe. https://localhost:8443/#/"; width="100%" height="600"> The X-Frame-Options HTTP response header can be used to indicate whether or not a browser should be allowed to render a page in a or . Sites can use this to avoid Clickjacking attacks, by ensuring that their content is not embedded into other sites. Set the X-Frame-Options header for all responses containing HTML content. The possible values are "DENY", "SAMEORIGIN", or "ALLOW-FROM uri" *X-Frame-Options Header Types* There are three possible values for the X-Frame-Options header: *DENY*, which prevents any domain from framing the content. The "DENY" setting is recommended unless a specific need has been identified for framing. *SAMEORIGIN*, which only allows the current site to frame the content. *ALLOW-FROM uri*, which permits the specified 'uri' to frame this page. (e.g., ALLOW-FROM http://www.example.com). -- This message was sent by Atlassian JIRA (v6.4.14#64029)
[GitHub] zeppelin issue #2293: [ZEPPELIN-2461] Masking Jetty Server version with User...
Github user krishna-pandey commented on the issue: https://github.com/apache/zeppelin/pull/2293 @prabhjyotsingh Jenkins job is successful. @Leemoonsoo, @felixcheung, @jongyoul Can you help review this? --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin pull request #2293: [ZEPPELIN-2461] Masking Jetty Server version wi...
Github user krishna-pandey closed the pull request at: https://github.com/apache/zeppelin/pull/2293 --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin pull request #2293: [ZEPPELIN-2461] Masking Jetty Server version wi...
GitHub user krishna-pandey reopened a pull request: https://github.com/apache/zeppelin/pull/2293 [ZEPPELIN-2461] Masking Jetty Server version with User-configurable parameter ### What is this PR for? Security conscious organisations does not want to reveal the Application Server name and version to prevent Script-kiddies from finding the information easily when fingerprinting the Application. The exact version number can tell an Attacker if the current Application Server is patched for or vulnerable to certain publicly known CVE associated to it. ### What type of PR is it? [Improvement | Feature] ### What is the Jira issue? * [ZEPPELIN-2461](https://issues.apache.org/jira/browse/ZEPPELIN-2461) ### How should this be tested? Providing a value in zeppelin-site.xml will replace the actual Jetty server version found in HTTP Header with provided value. E.g. - edit zeppelin-site.xml and add a property `zeppelin.server.jetty.name` and with value say `TOMCAT` - restart the server - open the app in browser then observe the Response Headers for the key "Server" this should now reflect "TOMCAT" ### Screenshots (if appropriate) ### Questions: * Does the licenses files need update? N/A * Is there breaking changes for older versions? N/A * Does this needs documentation? N/A You can merge this pull request into a Git repository by running: $ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2461 Alternatively you can review and apply these changes as the patch at: https://github.com/apache/zeppelin/pull/2293.patch To close this pull request, make a commit to your master/trunk branch with (at least) the following in the commit message: This closes #2293 commit b071f7ad05ae36a7734bb0906b6f6e61cb688647 Author: krishna-pandey Date: 2017-04-27T10:44:33Z Set App Server name to config value --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[GitHub] zeppelin pull request #2293: [ZEPPELIN-2461] Masking Jetty Server version wi...
GitHub user krishna-pandey opened a pull request: https://github.com/apache/zeppelin/pull/2293 [ZEPPELIN-2461] Masking Jetty Server version with User-configurable parameter ### What is this PR for? Security conscious organisations does not want to reveal the Application Server name and version to prevent Script-kiddies from finding the information easily when fingerprinting the Application. The exact version number can tell an Attacker if the current Application Server is patched for or vulnerable to certain publicly known CVE associated to it. ### What type of PR is it? [Improvement | Feature] ### What is the Jira issue? * [ZEPPELIN-2461](https://issues.apache.org/jira/browse/ZEPPELIN-2461) ### How should this be tested? Providing a value in zeppelin-site.xml will replace the actual Jetty server version found in HTTP Header with provided value. E.g. - edit zeppelin-site.xml and add a property `zeppelin.server.jetty.name` and with value say `TOMCAT` - restart the server - open the app in browser then observe the Response Headers for the key "Server" this should now reflect "TOMCAT" ### Screenshots (if appropriate) ### Questions: * Does the licenses files need update? N/A * Is there breaking changes for older versions? N/A * Does this needs documentation? N/A You can merge this pull request into a Git repository by running: $ git pull https://github.com/krishna-pandey/zeppelin ZEPPELIN-2461 Alternatively you can review and apply these changes as the patch at: https://github.com/apache/zeppelin/pull/2293.patch To close this pull request, make a commit to your master/trunk branch with (at least) the following in the commit message: This closes #2293 commit cf65c89d7fc61af5a7d045546b0b9175acc61af6 Author: krishna-pandey Date: 2017-04-27T10:44:33Z Set App Server name to config value --- If your project is set up for it, you can reply to this email and have your reply appear on GitHub as well. If your project does not have this feature enabled and wishes so, or if the feature is enabled but not working, please contact infrastructure at infrastruct...@apache.org or file a JIRA ticket with INFRA. ---
[jira] [Created] (ZEPPELIN-2461) Masking Jetty Server version with User-configurable parameter
Krishna Pandey created ZEPPELIN-2461: Summary: Masking Jetty Server version with User-configurable parameter Key: ZEPPELIN-2461 URL: https://issues.apache.org/jira/browse/ZEPPELIN-2461 Project: Zeppelin Issue Type: Bug Components: Core Affects Versions: 0.7.0 Environment: All Reporter: Krishna Pandey Priority: Minor Security conscious organisations does not want to reveal the Application Server name and version to prevent Script-kiddies from finding the information easily when fingerprinting the Application. The exact version number can tell an Attacker if the current Application Server is patched for or vulnerable to certain publicly known CVE associated to it. -- This message was sent by Atlassian JIRA (v6.3.15#6346)
