[Freeipa-devel] [freeipa PR#768][comment] Ticket#6854 caless
URL: https://github.com/freeipa/freeipa/pull/768 Title: #768: Ticket#6854 caless abbra commented: """ PKINIT certificates are using by `krb5kdc` which uses OpenSSL. It means they cannot be placed in an NSSDB. """ See the full comment at https://github.com/freeipa/freeipa/pull/768#issuecomment-300203017 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#756][comment] Added plugins directory to paclient subpackages
URL: https://github.com/freeipa/freeipa/pull/756 Title: #756: Added plugins directory to paclient subpackages abbra commented: """ Note that we want this fix in 4.4 branch as well -- it affects F25. """ See the full comment at https://github.com/freeipa/freeipa/pull/756#issuecomment-299089291 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#751][+ack] ipa-client-install: remove extra space in pkinit_anchors definition
URL: https://github.com/freeipa/freeipa/pull/751 Title: #751: ipa-client-install: remove extra space in pkinit_anchors definition Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#751][comment] ipa-client-install: remove extra space in pkinit_anchors definition
URL: https://github.com/freeipa/freeipa/pull/751 Title: #751: ipa-client-install: remove extra space in pkinit_anchors definition abbra commented: """ LGTM. For the record, this is broken since cf1c4e84e74ea15fe5cf7219872cf131bd53281e which is in 4.5.0 release. So we need to backport this to 4.5 branch. """ See the full comment at https://github.com/freeipa/freeipa/pull/751#issuecomment-298587034 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#724][comment] upgrade: adtrust update_tdo_gidnumber plugin must check if adtrust is…
URL: https://github.com/freeipa/freeipa/pull/724 Title: #724: upgrade: adtrust update_tdo_gidnumber plugin must check if adtrust is… abbra commented: """ LGTM """ See the full comment at https://github.com/freeipa/freeipa/pull/724#issuecomment-295855495 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#724][+ack] upgrade: adtrust update_tdo_gidnumber plugin must check if adtrust is…
URL: https://github.com/freeipa/freeipa/pull/724 Title: #724: upgrade: adtrust update_tdo_gidnumber plugin must check if adtrust is… Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#694][comment] RFC: implement local PKINIT deployment in server/replica install
URL: https://github.com/freeipa/freeipa/pull/694 Title: #694: RFC: implement local PKINIT deployment in server/replica install abbra commented: """ Yep. Then this PR can be merged once you removed distinction external/full. """ See the full comment at https://github.com/freeipa/freeipa/pull/694#issuecomment-295731813 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#694][comment] RFC: implement local PKINIT deployment in server/replica install
URL: https://github.com/freeipa/freeipa/pull/694 Title: #694: RFC: implement local PKINIT deployment in server/replica install abbra commented: """ I agree that it is internal detail whether we use local pkinit or not. However, we need to know that it is existing as oposed to not existing at all for older systems where we are going to perform upgrades. However, as you can derive this information by presence or lack of actual KDC certificate file in the file system during upgrade, this can be reduced, indeed. One more detail: we already have pkinit plugin (`ipaserver/plugins/pkinit.py`) which has `ipa pkinit-anonymous enable/disable` command. This command cannot now be used because even for 'local' case we require anonymous PKINIT to be usable and this means we cannot disable the principal. Perhaps, you can remove this command and add instead `ipa pkinit-status` command to show the status? It would show list of KDCs and their status. """ See the full comment at https://github.com/freeipa/freeipa/pull/694#issuecomment-295696911 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#694][+ack] RFC: implement local PKINIT deployment in server/replica install
URL: https://github.com/freeipa/freeipa/pull/694 Title: #694: RFC: implement local PKINIT deployment in server/replica install Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#694][comment] RFC: implement local PKINIT deployment in server/replica install
URL: https://github.com/freeipa/freeipa/pull/694 Title: #694: RFC: implement local PKINIT deployment in server/replica install abbra commented: """ I read through the code and I believe it addresses all use cases we have been discussing. LGTM. """ See the full comment at https://github.com/freeipa/freeipa/pull/694#issuecomment-295613748 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes abbra commented: """ Well, given that it is not officially supported yet, go ahead. """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-295195255 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#716][comment] Fix minor typos
URL: https://github.com/freeipa/freeipa/pull/716 Title: #716: Fix minor typos abbra commented: """ Thanks for this pull request. There are no tickets associated with these changes. The changes themselves are controversial. Do not change `--forwarder-*` to `--forward-*` because you are dealing with well-known DNS term here, not a simple word. Please normalize your `From:` line to be from the same email address. We do not accept something like `From: user <user@e5720.Speedport_W_724V_Typ_A_05011603_05_020>` Updates to translations should be done via https://fedora.zanata.org/project/view/freeipa?dswid=2118, see https://fedoraproject.org/wiki/L10N/Translate_on_Zanata for details. Changes like `plugable` -> `pluggable` may be OK in the text when they are part of a normal sentence. However, do not change the code itself and references in the text to those code names. These constitute part of a released plugin API and should not be changed. """ See the full comment at https://github.com/freeipa/freeipa/pull/716#issuecomment-294407938 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#709][+ack] Fix s4u2self with adtrust
URL: https://github.com/freeipa/freeipa/pull/709 Title: #709: Fix s4u2self with adtrust Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][synchronized] ipaserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: ipaserver/dcerpc: unify error processing
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From 25d8a94c862c51300198ea4956842521935e53f8 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH 1/2] ipaserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
Fixes https://pagure.io/freeipa/issue/6859
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
From 3846d72b7f202a281cfa833156a8dc7b2f61344d Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 5 Apr 2017 12:37:10 +0300
Subject: [PATCH 2/2] trust: always use oddjobd helper for fetching trust
information
Since introduction of privilege separation in IPA framework none of the
operations that require direct access to the framework's credentials can
be done. All authentication has to be performed with GSSAPI.
As result, we cannot obtain TGT for HTTP/.. principal with kinit
anymore, so it is better to re-route all types of trust to oddjobd
helper and get rid of casing out two-way trust.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438366
---
ipaserver/plugins/trust.py | 43 ++
[Freeipa-devel] [freeipa PR#682][synchronized] ipaserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: ipaserver/dcerpc: unify error processing
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From 25d8a94c862c51300198ea4956842521935e53f8 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH 1/2] ipaserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
Fixes https://pagure.io/freeipa/issue/6859
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
From 4f6054693e797215192388188b0b889342882dcf Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 5 Apr 2017 12:37:10 +0300
Subject: [PATCH 2/2] trust: always use oddjobd helper for fetching trust
information
Since introduction of privilege separation in IPA framework none of the
operations that require direct access to the framework's credentials can
be done. All authentication has to be performed with GSSAPI.
As result, we cannot obtain TGT for HTTP/.. principal with kinit
anymore, so it is better to re-route all types of trust to oddjobd
helper and get rid of casing out two-way trust.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438366
---
ipaserver/plugins/trust.py | 42 +---
[Freeipa-devel] [freeipa PR#682][edited] ipaserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682 Author: abbra Title: #682: ipaserver/dcerpc: unify error processing Action: edited Changed field: title Original value: """ ipserver/dcerpc: unify error processing """ -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][synchronized] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: ipserver/dcerpc: unify error processing
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From 25d8a94c862c51300198ea4956842521935e53f8 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH 1/2] ipaserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
Fixes https://pagure.io/freeipa/issue/6859
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
From 662914834ebe3b75a85f66ebc4ef95315f9683f0 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 5 Apr 2017 12:37:10 +0300
Subject: [PATCH 2/2] trust: always use oddjobd helper for fetching trust
information
Since introduction of privilege separation in IPA framework none of the
operations that require direct access to the framework's credentials can
be done. All authentication has to be performed with GSSAPI.
As result, we cannot obtain TGT for HTTP/.. principal with kinit
anymore, so it is better to re-route all types of trust to oddjobd
helper and get rid of casing out two-way trust.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438366
---
ipaserver/plugins/trust.py | 38 +++---
[Freeipa-devel] [freeipa PR#682][synchronized] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: ipserver/dcerpc: unify error processing
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From 4601201f919ebf97e2ea82bd8c5f66ee23a8aa6d Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH 1/2] ipserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
Fixes https://pagure.io/freeipa/issue/6859
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
From db9bff4ecc184f359b858119ba5e8cfc9c8a635f Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 5 Apr 2017 12:37:10 +0300
Subject: [PATCH 2/2] trust: always use oddjobd helper for fetching trust
information
Since introduction of privilege separation in IPA framework none of the
operations that require direct access to the framework's credentials can
be done. All authentication has to be performed with GSSAPI.
As result, we cannot obtain TGT for HTTP/.. principal with kinit
anymore, so it is better to re-route all types of trust to oddjobd
helper and get rid of casing out two-way trust.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438366
---
ipaserver/plugins/trust.py | 38 +++---
[Freeipa-devel] [freeipa PR#699][comment] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes abbra commented: """ Ok, so far I cannot build a wheel from git repo on Mac OS X as we have a number of limitations ourselves -- we need to fix our configure to allow just generating enough of `ipasetup.py` and make files to run python wheels code. I'll supply a separate PR for this. """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292927905 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes abbra commented: """ I still need to test the whole set on Mac OS X myself as we have no way to test that in CI. Thus, this PR will depend on me (or some one else from FreeIPA team) to actually test the code on Mac OS X. """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292880002 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes abbra commented: """ Note that we need something similar to https://github.com/untitaker/python-atomicwrites/commit/2bdd9dae62b7434c7b2383ce45fb515bdf70c3c3 to behave properly on Mac OS X. """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292864166 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes abbra commented: """ Please don't set ACK yet, I'm not finished with review. I do not want to replace fdatasync() with fsync(), this is not correct towards other platforms. I haven't yet tested this pull request against Mac OS X, so do not set ACK yet. """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292862967 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][-ack] ipaclient/ipapython macOS compatibility fixes
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: ipaclient/ipapython macOS compatibility fixes Label: -ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][edited] [WIP] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682 Author: abbra Title: #682: [WIP] ipserver/dcerpc: unify error processing Action: edited Changed field: title Original value: """ [WIP] ipserver/dcerpc: unify error processing """ -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][comment] [WIP] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682 Title: #682: [WIP] ipserver/dcerpc: unify error processing abbra commented: """ Updated patches and descriptions to include bug references. """ See the full comment at https://github.com/freeipa/freeipa/pull/682#issuecomment-292545612 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][synchronized] [WIP] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: [WIP] ipserver/dcerpc: unify error processing
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From b0583338006e86ebc9beb4b9c171e123efd970fc Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH 1/2] ipserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438348
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
From dbbc875873b81bc14b6027d9c45b53f873608529 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 5 Apr 2017 12:37:10 +0300
Subject: [PATCH 2/2] trust: always use oddjobd helper for fetching trust
information
Since introduction of privilege separation in IPA framework none of the
operations that require direct access to the framework's credentials can
be done. All authentication has to be performed with GSSAPI.
As result, we cannot obtain TGT for HTTP/.. principal with kinit
anymore, so it is better to re-route all types of trust to oddjobd
helper and get rid of casing out two-way trust.
Fixes https://bugzilla.redhat.com/show_bug.cgi?id=1438366
---
ipaserver/plugins/trust.py | 36
[Freeipa-devel] [freeipa PR#699][comment] Fix libkrb5 filename for macOS
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: Fix libkrb5 filename for macOS abbra commented: """ There is a PEP8 error: PEP-8 errors: ./ipapython/session_storage.py:11:21: E225 missing whitespace around operator """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292527976 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] Fix libkrb5 filename for macOS
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: Fix libkrb5 filename for macOS abbra commented: """ Ok. Let me look at it next week when I'll have time. Could you please add a short step by step instruction how you configured IPA client on Mac OS X? """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292527660 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#699][comment] Fix libkrb5 filename for macOS
URL: https://github.com/freeipa/freeipa/pull/699 Title: #699: Fix libkrb5 filename for macOS abbra commented: """ Thanks. Do you have IPA client code working on Mac OS X? """ See the full comment at https://github.com/freeipa/freeipa/pull/699#issuecomment-292523505 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#632][comment] ipa-sam: create the gidNumber attribute in the trusted domain entry
URL: https://github.com/freeipa/freeipa/pull/632 Title: #632: ipa-sam: create the gidNumber attribute in the trusted domain entry abbra commented: """ LGTM. `nltest /sc_verify:ipa.example.test` works thanks to this pull request: ``` C:\Users\Administrator>nltest /sc_query:ipa.example.test Flags: 30 HAS_IP HAS_TIMESERV Trusted DC Name \\master.ipa.example.test Trusted DC Connection Status Status = 0 0x0 NERR_Success The command completed successfully ``` """ See the full comment at https://github.com/freeipa/freeipa/pull/632#issuecomment-292167012 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#632][+ack] ipa-sam: create the gidNumber attribute in the trusted domain entry
URL: https://github.com/freeipa/freeipa/pull/632 Title: #632: ipa-sam: create the gidNumber attribute in the trusted domain entry Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#632][comment] ipa-sam: create the gidNumber attribute in the trusted domain entry
URL: https://github.com/freeipa/freeipa/pull/632 Title: #632: ipa-sam: create the gidNumber attribute in the trusted domain entry abbra commented: """ Thanks. I read through the code and it looks good to me. I'm going to test it together with my work on ipasam_update_sam_account() tomorrow. """ See the full comment at https://github.com/freeipa/freeipa/pull/632#issuecomment-291249140 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][comment] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682 Title: #682: ipserver/dcerpc: unify error processing abbra commented: """ Note: this is WIP, I'm waiting for Sudhir to provide a bug and logs that show the changes he encountered when running existing test suite against Samba 4.6.2. """ See the full comment at https://github.com/freeipa/freeipa/pull/682#issuecomment-291070811 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#682][opened] ipserver/dcerpc: unify error processing
URL: https://github.com/freeipa/freeipa/pull/682
Author: abbra
Title: #682: ipserver/dcerpc: unify error processing
Action: opened
PR body:
"""
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
"""
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/682/head:pr682
git checkout pr682
From 542ec3f1191e37f994806e292ee1f46047a8345e Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 3 Apr 2017 10:29:21 +0300
Subject: [PATCH] ipserver/dcerpc: unify error processing
Samba error code reporting changes from version to version but we also
did not provide proper input into DCE RPC error processing method we
have.
Unify error processing and add few more fallback entries.
With Samba 4.7 we'll have to change it again because error code
processing for Samba Python modules will change with introduction of
samba.ntstatus and samba.werror modules.
Note that this commit also changes a message returned for error code
-1073741772 (NT_STATUS_OBJECT_NOT_FOUND) because it is more general one.
---
ipaserver/dcerpc.py | 23 +--
1 file changed, 17 insertions(+), 6 deletions(-)
diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py
index 2d9d7e5..d684a17 100644
--- a/ipaserver/dcerpc.py
+++ b/ipaserver/dcerpc.py
@@ -117,19 +117,27 @@ def is_sid_valid(sid):
# we simply will skip the binding
access_denied_error,
-1073741772: # NT_STATUS_OBJECT_NAME_NOT_FOUND
-errors.RemoteRetrieveError(
-reason=_('CIFS server configuration does not allow '
- 'access to pipe\\lsarpc')),
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
}
dcerpc_error_messages = {
"NT_STATUS_OBJECT_NAME_NOT_FOUND":
errors.NotFound(
reason=_('Cannot find specified domain or server name')),
+"The object name is not found.":
+errors.NotFound(
+reason=_('Cannot find specified domain or server name')),
"WERR_NO_LOGON_SERVERS":
errors.RemoteRetrieveError(
reason=_('AD DC was unable to reach any IPA domain controller. '
'Most likely it is a DNS or firewall issue')),
+# This is a very long key, don't change it
+"There are currently no logon servers available to "
+"service the logon request.":
+errors.RemoteRetrieveError(
+reason=_('AD DC was unable to reach any IPA domain controller. '
+ 'Most likely it is a DNS or firewall issue')),
"NT_STATUS_INVALID_PARAMETER_MIX":
errors.RequirementError(
name=_('At least the domain or IP address should be specified')),
@@ -802,7 +810,8 @@ def __retrieve_trusted_domain_gc_list(self, domain):
# Both methods should not fail at the same time
if finddc_error and len(info['gc']) == 0:
-raise assess_dcerpc_exception(message=str(finddc_error))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
self._info[domain] = info
return info
@@ -908,7 +917,8 @@ def retrieve_anonymously(self, remote_host,
else:
result = netrc.finddc(address=remote_host, flags=flags)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
if not result:
return False
@@ -1408,7 +1418,8 @@ def communicate(td):
result = netrc.finddc(domain=trustdomain,
flags=nbt.NBT_SERVER_LDAP | nbt.NBT_SERVER_DS)
except RuntimeError as e:
-raise assess_dcerpc_exception(message=str(e))
+num, message = e.args # pylint: disable=unpacking-non-sequence
+raise assess_dcerpc_exception(num=num, message=message)
td.info['dc'] = unicode(result.pdc_dns_name)
td.info['name'] = unicode(result.dns_domain)
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#672][comment] IPA-KDB: use relative path in ipa-certmap config snippet
URL: https://github.com/freeipa/freeipa/pull/672 Title: #672: IPA-KDB: use relative path in ipa-certmap config snippet abbra commented: """ > @sumit-bose What happens when the shared library is missing? Does 32bit kinit > fail or work on a X86_64 system when 32bit ipadb.so is missing? It is not about kinit. The module is for KDC, not client side. We guarantee it exists because we install it. """ See the full comment at https://github.com/freeipa/freeipa/pull/672#issuecomment-290317784 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#629][synchronized] adtrust: make sure that runtime hostname result is consistent with the configuration
URL: https://github.com/freeipa/freeipa/pull/629
Author: abbra
Title: #629: adtrust: make sure that runtime hostname result is consistent
with the configuration
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/629/head:pr629
git checkout pr629
From 195b5b98defa5ac3ad90d75bc411a315fccfdd52 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 20 Mar 2017 13:23:44 +0200
Subject: [PATCH] adtrust: make sure that runtime hostname result is consistent
with the configuration
FreeIPA's `ipasam` module to Samba uses gethostname() call to identify
own server's host name. This value is then used in multiple places,
including construction of cifs/host.name principal. `ipasam` module
always uses GSSAPI authentication when talking to LDAP, so Kerberos
keys must be available in the /etc/samba/samba.keytab. However, if
the principal was created using non-FQDN name but system reports
FQDN name, `ipasam` will fail to acquire Kerberos credentials.
Same with FQDN principal and non-FQDN hostname.
Also host name and principal name must have the same case.
Report an error when configuring ADTrust instance with inconsistent
runtime hostname and configuration. This prevents errors like this:
[20/21]: starting CIFS services
ipa : CRITICAL CIFS services failed to start
where samba logs have this:
[2017/03/20 06:34:27.385307, 0] ipa_sam.c:4193(bind_callback_cleanup)
kerberos error: code=-1765328203, message=Keytab contains no suitable keys for cifs/ipatr...@example.com
[2017/03/20 06:34:27.385476, 1] ../source3/lib/smbldap.c:1206(get_cached_ldap_connect)
Connection to LDAP server failed for the 16 try!
Fixes https://pagure.io/freeipa/issue/6786
---
ipaserver/install/adtrustinstance.py | 12
1 file changed, 12 insertions(+)
diff --git a/ipaserver/install/adtrustinstance.py b/ipaserver/install/adtrustinstance.py
index 0b18985..b4db055 100644
--- a/ipaserver/install/adtrustinstance.py
+++ b/ipaserver/install/adtrustinstance.py
@@ -27,6 +27,7 @@
import string
import struct
import re
+import socket
import six
@@ -689,6 +690,15 @@ def __enable_compat_tree(self):
except Exception as e:
root_logger.critical("Enabling nsswitch support in slapi-nis failed with error '%s'" % e)
+def __validate_server_hostname(self):
+hostname = socket.gethostname()
+if hostname != self.fqdn:
+raise ValueError("Host reports different name than configured: "
+ "'%s' versus '%s'. Samba requires to have "
+ "the same hostname or Kerberos principal "
+ "'cifs/%s' will not be found in Samba keytab." %
+ (hostname, self.fqdn, self.fqdn))
+
def __start(self):
try:
self.start()
@@ -804,6 +814,8 @@ def find_local_id_range(self):
api.Backend.ldap2.add_entry(entry)
def create_instance(self):
+self.step("validate server hostname",
+ self.__validate_server_hostname)
self.step("stopping smbd", self.__stop)
self.step("creating samba domain object", \
self.__create_samba_domain_object)
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#629][comment] adtrust: make sure that runtime hostname result is consistent with the configuration
URL: https://github.com/freeipa/freeipa/pull/629 Title: #629: adtrust: make sure that runtime hostname result is consistent with the configuration abbra commented: """ Removed backslashes and also moved the check to be the first step when creating an instance. """ See the full comment at https://github.com/freeipa/freeipa/pull/629#issuecomment-290086797 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#629][synchronized] adtrust: make sure that runtime hostname result is consistent with the configuration
URL: https://github.com/freeipa/freeipa/pull/629
Author: abbra
Title: #629: adtrust: make sure that runtime hostname result is consistent
with the configuration
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/629/head:pr629
git checkout pr629
From f79ec2d56bc8a16765633156a11d4cd9210795d9 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 20 Mar 2017 13:23:44 +0200
Subject: [PATCH] adtrust: make sure that runtime hostname result is consistent
with the configuration
FreeIPA's `ipasam` module to Samba uses gethostname() call to identify
own server's host name. This value is then used in multiple places,
including construction of cifs/host.name principal. `ipasam` module
always uses GSSAPI authentication when talking to LDAP, so Kerberos
keys must be available in the /etc/samba/samba.keytab. However, if
the principal was created using non-FQDN name but system reports
FQDN name, `ipasam` will fail to acquire Kerberos credentials.
Same with FQDN principal and non-FQDN hostname.
Also host name and principal name must have the same case.
Report an error when configuring ADTrust instance with inconsistent
runtime hostname and configuration. This prevents errors like this:
[20/21]: starting CIFS services
ipa : CRITICAL CIFS services failed to start
where samba logs have this:
[2017/03/20 06:34:27.385307, 0] ipa_sam.c:4193(bind_callback_cleanup)
kerberos error: code=-1765328203, message=Keytab contains no suitable keys for cifs/ipatr...@example.com
[2017/03/20 06:34:27.385476, 1] ../source3/lib/smbldap.c:1206(get_cached_ldap_connect)
Connection to LDAP server failed for the 16 try!
Fixes https://pagure.io/freeipa/issue/6786
---
ipaserver/install/adtrustinstance.py | 11 +++
1 file changed, 11 insertions(+)
diff --git a/ipaserver/install/adtrustinstance.py b/ipaserver/install/adtrustinstance.py
index 0b18985..3527ca9 100644
--- a/ipaserver/install/adtrustinstance.py
+++ b/ipaserver/install/adtrustinstance.py
@@ -689,6 +689,15 @@ def __enable_compat_tree(self):
except Exception as e:
root_logger.critical("Enabling nsswitch support in slapi-nis failed with error '%s'" % e)
+def __validate_server_hostname(self):
+hostname = socket.gethostname()
+if hostname != self.fqdn:
+raise ValueError("Host reports different name than configured: "
+ "'%s' versus '%s'. Samba requires to have "
+ "the same hostname or Kerberos principal "
+ "'cifs/%s' will not be found in Samba keytab." %
+ (hostname, self.fqdn, self.fqdn))
+
def __start(self):
try:
self.start()
@@ -804,6 +813,8 @@ def find_local_id_range(self):
api.Backend.ldap2.add_entry(entry)
def create_instance(self):
+self.step("validate server hostname",
+ self.__validate_server_hostname)
self.step("stopping smbd", self.__stop)
self.step("creating samba domain object", \
self.__create_samba_domain_object)
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#669][comment] server: make sure we test for sss_nss_getlistbycert
URL: https://github.com/freeipa/freeipa/pull/669 Title: #669: server: make sure we test for sss_nss_getlistbycert abbra commented: """ On the systems where pkg-config is available, positive result from pkg-config check means headers are available because pkg-config files are part of development sub-packages. Symbol check in a library is enough then. """ See the full comment at https://github.com/freeipa/freeipa/pull/669#issuecomment-290016098 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#668][comment] spec file: bump libsss_nss_idmap-devel BuildRequires
URL: https://github.com/freeipa/freeipa/pull/668 Title: #668: spec file: bump libsss_nss_idmap-devel BuildRequires abbra commented: """ I submitted https://github.com/freeipa/freeipa/pull/669 for that """ See the full comment at https://github.com/freeipa/freeipa/pull/668#issuecomment-290010251 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#669][opened] server: make sure we test for sss_nss_getlistbycert
URL: https://github.com/freeipa/freeipa/pull/669 Author: abbra Title: #669: server: make sure we test for sss_nss_getlistbycert Action: opened PR body: """ Fixes https://pagure.io/freeipa/issue/6828 """ To pull the PR as Git branch: git remote add ghfreeipa https://github.com/freeipa/freeipa git fetch ghfreeipa pull/669/head:pr669 git checkout pr669 From ffca2ba3b77e77bc89e80f48f4a2abe93b70732f Mon Sep 17 00:00:00 2001 From: Alexander Bokovoy <aboko...@redhat.com> Date: Wed, 29 Mar 2017 10:43:11 +0300 Subject: [PATCH] server: make sure we test for sss_nss_getlistbycert Fixes https://pagure.io/freeipa/issue/6828 --- server.m4 | 5 + 1 file changed, 5 insertions(+) diff --git a/server.m4 b/server.m4 index 5d5333e..346d73e 100644 --- a/server.m4 +++ b/server.m4 @@ -29,6 +29,11 @@ DIRSRV_CFLAGS="$DIRSRV_CFLAGS $NSPR_CFLAGS" dnl -- sss_idmap is needed by the extdom exop -- PKG_CHECK_MODULES([SSSIDMAP], [sss_idmap]) PKG_CHECK_MODULES([SSSNSSIDMAP], [sss_nss_idmap >= 1.15.2]) +AC_CHECK_LIB([sss_nss_idmap], + [sss_nss_getlistbycert], + [], + [AC_MSG_ERROR([Required sss_nss_getlistbycert symbol in sss_nss_idmap not found])], + []) dnl -- sss_certmap and certauth.h are needed by the IPA KDB certauth plugin -- PKG_CHECK_EXISTS([sss_certmap], -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#668][comment] spec file: bump libsss_nss_idmap-devel BuildRequires
URL: https://github.com/freeipa/freeipa/pull/668 Title: #668: spec file: bump libsss_nss_idmap-devel BuildRequires abbra commented: """ No, It will make downstream harder because RHEL downstream will only have 1.15.2 with patches on top of that version. I have a pull request coming that actually checks for a specific function we know is part of those SSSD patches. """ See the full comment at https://github.com/freeipa/freeipa/pull/668#issuecomment-290009593 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#649][+ack] Session cookie storage and handling fixes
URL: https://github.com/freeipa/freeipa/pull/649 Title: #649: Session cookie storage and handling fixes Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#649][comment] Session cookie storage and handling fixes
URL: https://github.com/freeipa/freeipa/pull/649 Title: #649: Session cookie storage and handling fixes abbra commented: """ LGTM to me. @simo5 explained that `expiry=...` substring is part of the actual cookie `mod_session` adds (it is timestamp in nanonseconds) -- Cookie class does not see it, so it has to be removed separately in the last commit. """ See the full comment at https://github.com/freeipa/freeipa/pull/649#issuecomment-289445234 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#640][comment] Remove pkinit options from master/replica on DL0
URL: https://github.com/freeipa/freeipa/pull/640 Title: #640: Remove pkinit options from master/replica on DL0 abbra commented: """ Good question. I think we should remove all mentioning of PKINIT options for DL0 and explicitly configure local CA there. On DL1 we already require to provide pkinit cert for CA-less setup. However, there we should treat --no-pkinit as use of local CA (certmonger's one). """ See the full comment at https://github.com/freeipa/freeipa/pull/640#issuecomment-289041029 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#617][comment] Allow renaming of sudo and HBAC rules
URL: https://github.com/freeipa/freeipa/pull/617 Title: #617: Allow renaming of sudo and HBAC rules abbra commented: """ I haven't seen any custom plugin that used `rdn_is_private_key`. We can document the change in release notes. """ See the full comment at https://github.com/freeipa/freeipa/pull/617#issuecomment-289022375 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#649][comment] Session cookie storage and handling fixes
URL: https://github.com/freeipa/freeipa/pull/649 Title: #649: Session cookie storage and handling fixes abbra commented: """ @simo5, I think I found why it happened -- I actually had krbMaxTicketLife set for HTTP/... principal to 300 seconds. So I think your patches are good. I'd like you to fix fourth patch according to inline comments I left but that's it. """ See the full comment at https://github.com/freeipa/freeipa/pull/649#issuecomment-288963636 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#639][comment] WebUI: Login for AD Users
URL: https://github.com/freeipa/freeipa/pull/639 Title: #639: WebUI: Login for AD Users abbra commented: """ LGTM and works just fine: 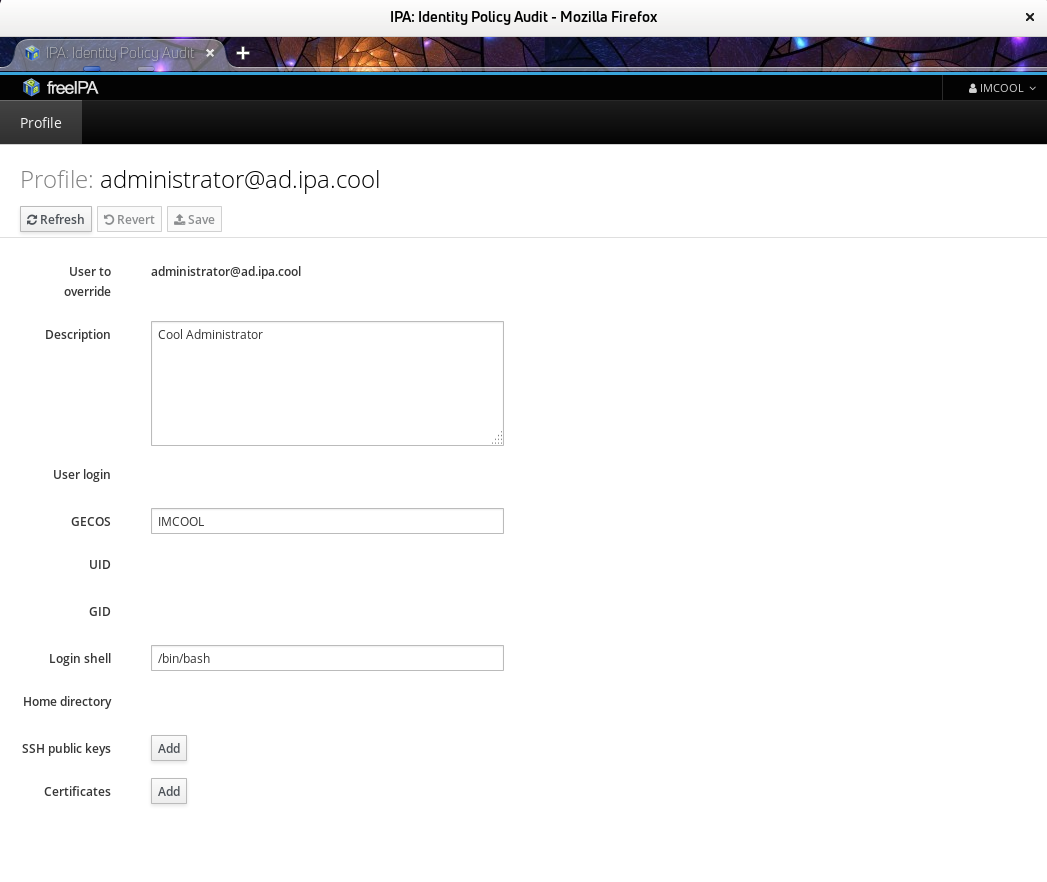 """ See the full comment at https://github.com/freeipa/freeipa/pull/639#issuecomment-288956595 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#649][comment] Session cookie storage and handling fixes
URL: https://github.com/freeipa/freeipa/pull/649 Title: #649: Session cookie storage and handling fixes abbra commented: """ I tested the whole patchset. It worked for me first time I've got cookie expired. However, it broke in ~10 minutes afterwards -- apparently, keyring ccache was empty, according to `klist`. After few more minutes I was able to list TGT from the same ccache and `ipa` CLI worked again. I suspect we created something that MIT Kerberos library does not really understand. ```text [10609] 1490339971.189122: Storing config in KEYRING:persistent:0:krb_ccache_uA6VDOR for ad...@xs.ipa.cool: X-IPA-Session-Cookie: ipa_session=MagBearerToken=NtVuqNjq7jKtuDiw9lDSxHI%2frs5vd4UZ9o1sSZjDAemTImufljlG66i3l6MgA%2fmxtC0kPQgUqUEVcFJ04GWKOzK%2bYeTTEeAXrs59sNUq4VZzmRDTbLW%2by9ccodzlUdoeIiDVKdJsGHlBKyKTtcm1UW0a0LY%2bQLJscOQImQOlNpJ%2bxFs3szGU5w1rFbjQPwp6\x00 [10609] 1490339971.189156: Storing ad...@xs.ipa.cool -> krb5_ccache_conf_data/X-IPA-Session-Cookie/admin\@XS.IPA.COOL@X-CACHECONF: in KEYRING:persistent:0:krb_ccache_uA6VDOR ``` ... some time later, in a different execution of ipa user-show ... ```text ipa: DEBUG: New HTTP connection (nyx.xs.ipa.cool) ipa: DEBUG: HTTP connection destroyed (nyx.xs.ipa.cool) Traceback (most recent call last): File "/usr/lib/python2.7/site-packages/ipalib/rpc.py", line 676, in single_request self.get_auth_info() File "/usr/lib/python2.7/site-packages/ipalib/rpc.py", line 628, in get_auth_info self._handle_exception(e, service=service) File "/usr/lib/python2.7/site-packages/ipalib/rpc.py", line 585, in _handle_exception raise errors.CCacheError() CCacheError: did not receive Kerberos credentials ipa: DEBUG: Destroyed connection context.rpcclient_140537682029648 ipa: ERROR: did not receive Kerberos credentials [root@nyx ~]# klist Ticket cache: KEYRING:persistent:0:krb_ccache_uA6VDOR Default principal: ad...@xs.ipa.cool Valid starting Expires Service principal klist: No credentials cache found while retrieving a ticket ``` some time afterwards, without running kinit ```text [root@nyx ~]# klist Ticket cache: KEYRING:persistent:0:krb_ccache_uA6VDOR Default principal: ad...@xs.ipa.cool Valid starting Expires Service principal 03/24/2017 08:07:02 03/25/2017 08:06:56 krbtgt/xs.ipa.c...@xs.ipa.cool ``` and running ipa user-show now succeeds in retrieving old cookie, invalidating it, negotiating a new one, and storing it ```text [10747] 1490340689.131026: Storing config in KEYRING:persistent:0:krb_ccache_uA6VDOR for ad...@xs.ipa.cool: X-IPA-Session-Cookie: ipa_session=MagBearerToken=J9aCtYUAsRFpJJhrMu4x4E2gwA2ojJOPdYT7iN7GtTyec7%2fj9lW1LyzgpLhjawaCa9MsK%2btOPDF6mKTsCSJqey3vhgY35ezg8Cwzbln6yGr0kPfDCWoxSQGYWx%2fSSIRVltu8akoXu1NvzP1%2bF0NEFrdzGi2%2bZDZXRFvUC5UpLg%2b3JMg5ZNExYlr%2bLHHQpAJh\x00 [10747] 1490340689.131071: Storing ad...@xs.ipa.cool -> krb5_ccache_conf_data/X-IPA-Session-Cookie/admin\@XS.IPA.COOL@X-CACHECONF: in KEYRING:persistent:0:krb_ccache_uA6VDOR ``` """ See the full comment at https://github.com/freeipa/freeipa/pull/649#issuecomment-288954010 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#575][comment] IPA certauth plugin
URL: https://github.com/freeipa/freeipa/pull/575 Title: #575: IPA certauth plugin abbra commented: """ The code LGTM. Once updated SSSD is added to freeipa-master copr, let's see what CI says. Authentication indicators' handling would need to be added in a separate PR once certmap rules would provide the indicator value. """ See the full comment at https://github.com/freeipa/freeipa/pull/575#issuecomment-288686687 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#644][comment] extdom: improve certificate request
URL: https://github.com/freeipa/freeipa/pull/644 Title: #644: extdom: improve certificate request abbra commented: """ LGTM. I read the code but since SSSD counterpart is currently on review, travis fails the build. """ See the full comment at https://github.com/freeipa/freeipa/pull/644#issuecomment-288671714 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#638][comment] ipalib/rpc.py: Fix session handling for KEYRING: ccaches
URL: https://github.com/freeipa/freeipa/pull/638 Title: #638: ipalib/rpc.py: Fix session handling for KEYRING: ccaches abbra commented: """ Yes, KCM will work. However, I wonder if we could use a different approach by storing cookie in a fake ticket with a proper lifetime set to the cookie expiration. This would still get multiple entries added for FILE: case but at least will allow us to return most recent one. """ See the full comment at https://github.com/freeipa/freeipa/pull/638#issuecomment-288408872 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#617][comment] Allow renaming of sudo and HBAC rules
URL: https://github.com/freeipa/freeipa/pull/617 Title: #617: Allow renaming of sudo and HBAC rules abbra commented: """ I like the idea but please address @HonzaCholasta comments. """ See the full comment at https://github.com/freeipa/freeipa/pull/617#issuecomment-288411495 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#637][synchronized] ldap2: use LDAP whoami operation to retrieve bind DN for current connection
URL: https://github.com/freeipa/freeipa/pull/637
Author: abbra
Title: #637: ldap2: use LDAP whoami operation to retrieve bind DN for current
connection
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/637/head:pr637
git checkout pr637
From 3f92253780de9f553bae3bc2294214a6dbcd6eb3 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 22 Mar 2017 13:00:22 +0200
Subject: [PATCH] ldap2: use LDAP whoami operation to retrieve bind DN for
current connection
For external users which are mapped to some DN in LDAP server, we
wouldn't neccesary be able to find a kerberos data in their LDAP entry.
Instead of searching for Kerberos principal use actual DN we are bound
to because for get_effective_rights LDAP control we only need the DN
itself.
Fixes https://pagure.io/freeipa/issue/6797
---
ipaserver/plugins/ldap2.py | 7 +++
1 file changed, 3 insertions(+), 4 deletions(-)
diff --git a/ipaserver/plugins/ldap2.py b/ipaserver/plugins/ldap2.py
index def1245..3b1e4da 100644
--- a/ipaserver/plugins/ldap2.py
+++ b/ipaserver/plugins/ldap2.py
@@ -286,12 +286,11 @@ def get_effective_rights(self, dn, attrs_list):
assert isinstance(dn, DN)
-principal = getattr(context, 'principal')
-entry = self.find_entry_by_attr("krbprincipalname", principal,
-"krbPrincipalAux", base_dn=self.api.env.basedn)
+bind_dn = self.conn.whoami_s()[4:]
+
sctrl = [
GetEffectiveRightsControl(
-True, "dn: {0}".format(entry.dn).encode('utf-8'))
+True, "dn: {0}".format(bind_dn).encode('utf-8'))
]
self.conn.set_option(_ldap.OPT_SERVER_CONTROLS, sctrl)
try:
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#637][comment] ldap2: use LDAP whoami operation to retrieve bind DN for current connection
URL: https://github.com/freeipa/freeipa/pull/637 Title: #637: ldap2: use LDAP whoami operation to retrieve bind DN for current connection abbra commented: """ Removed try: finally: block, I agree that it is better to propagate error up the stack. """ See the full comment at https://github.com/freeipa/freeipa/pull/637#issuecomment-288404454 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#638][comment] ipalib/rpc.py: Fix session handling for KEYRING: ccaches
URL: https://github.com/freeipa/freeipa/pull/638 Title: #638: ipalib/rpc.py: Fix session handling for KEYRING: ccaches abbra commented: """ Note: this is WIP, please test it against KEYRING: ccaches. """ See the full comment at https://github.com/freeipa/freeipa/pull/638#issuecomment-288402486 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#638][opened] ipalib/rpc.py: Fix session handling for KEYRING: ccaches
URL: https://github.com/freeipa/freeipa/pull/638 Author: abbra Title: #638: ipalib/rpc.py: Fix session handling for KEYRING: ccaches Action: opened PR body: """ MIT Kerberos allows to store configuration entries in the ccache. Unfortunately, there are big differences between ccache types in how these entries behave: - MIT Kerberos FILE: ccache code does always append entries, so we end up with ever growing ccache files. In KEYRING: case we are lucky that add_key syscall actually updates the key with the same name. - MIT Kerberos FILE: and KEYRING: ccache code does not allow to remove cred from ccache. Corresponding functions simply return KRB5_CC_NOSUPP; As result, using FILE: ccache type does not allow us to override our session cookie stored as a config entry in the ccache. Successive runs of ipa CLI create new entries in the ccache and only return the original one. Once we put a cookie in the FILE: ccache, it cannot be removed from there and cannot be replaced. Also, as retrieval code in krb5_cc_get_conf() ends up calling krb5_cc_retrieve_cred() with 0 flags and only has a cred principal name constructed out of a our conf key (X-IPA-Session_Cookie), none of the matching logic for "most recent ticket" could be applied. This commit attempts to improve situation for KEYRING: ccache type by setting the cookie to a predefined 'empty' value when deleting config entry. This avoids non-working 'remove cred' code path in ccache processing in MIT Kerberos. Additionally, when server side denies our cookie, it sends us empty Negotiate value. We errorneously treat it as invalid token. We also must use proper method to initialize our connection, SSLTransport.make_connection knows nothing about setting up GSSAPI client context, KrbTransport does. Unfortunately, with non-removable session cookie the code to initialize session context never triggered properly after expire. Fixes https://pagure.io/freeipa/issue/6775 """ To pull the PR as Git branch: git remote add ghfreeipa https://github.com/freeipa/freeipa git fetch ghfreeipa pull/638/head:pr638 git checkout pr638 From de6d317bfb0f024847a212aab0e6c1026bc84d5c Mon Sep 17 00:00:00 2001 From: Alexander Bokovoy <aboko...@redhat.com> Date: Wed, 22 Mar 2017 12:23:02 +0200 Subject: [PATCH] ipalib/rpc.py: Fix session handling for KEYRING: ccaches MIT Kerberos allows to store configuration entries in the ccache. Unfortunately, there are big differences between ccache types in how these entries behave: - MIT Kerberos FILE: ccache code does always append entries, so we end up with ever growing ccache files. In KEYRING: case we are lucky that add_key syscall actually updates the key with the same name. - MIT Kerberos FILE: and KEYRING: ccache code does not allow to remove cred from ccache. Corresponding functions simply return KRB5_CC_NOSUPP; As result, using FILE: ccache type does not allow us to override our session cookie stored as a config entry in the ccache. Successive runs of ipa CLI create new entries in the ccache and only return the original one. Once we put a cookie in the FILE: ccache, it cannot be removed from there and cannot be replaced. Also, as retrieval code in krb5_cc_get_conf() ends up calling krb5_cc_retrieve_cred() with 0 flags and only has a cred principal name constructed out of a our conf key (X-IPA-Session_Cookie), none of the matching logic for "most recent ticket" could be applied. This commit attempts to improve situation for KEYRING: ccache type by setting the cookie to a predefined 'empty' value when deleting config entry. This avoids non-working 'remove cred' code path in ccache processing in MIT Kerberos. Additionally, when server side denies our cookie, it sends us empty Negotiate value. We errorneously treat it as invalid token. We also must use proper method to initialize our connection, SSLTransport.make_connection knows nothing about setting up GSSAPI client context, KrbTransport does. Unfortunately, with non-removable session cookie the code to initialize session context never triggered properly after expire. Fixes https://pagure.io/freeipa/issue/6775 --- ipalib/rpc.py | 20 +++- 1 file changed, 15 insertions(+), 5 deletions(-) diff --git a/ipalib/rpc.py b/ipalib/rpc.py index 303b22a..50b010d 100644 --- a/ipalib/rpc.py +++ b/ipalib/rpc.py @@ -92,6 +92,7 @@ COOKIE_NAME = 'ipa_session' CCACHE_COOKIE_KEY = 'X-IPA-Session-Cookie' +CCACHE_COOKIE_EMPTY_VALUE = 'X-IPA-Session-Cookie-Empty' errors_by_code = dict((e.errno, e) for e in public_errors) @@ -118,7 +119,10 @@ def read_persistent_client_session_data(principal): ''' try: -return session_storage.get_data(principal, CCACHE_COOKIE_KEY) +value = session_storage.get_data(principal, CCACHE_COOKIE_KEY) +if value == CCACHE_COOKIE_EMPTY_VALUE: +raise ValueError(CCACHE_COOKIE_EMPTY_VALUE) +return value
[Freeipa-devel] [freeipa PR#637][opened] ldap2: use LDAP whoami operation to retrieve bind DN for current connection
URL: https://github.com/freeipa/freeipa/pull/637
Author: abbra
Title: #637: ldap2: use LDAP whoami operation to retrieve bind DN for current
connection
Action: opened
PR body:
"""
For external users which are mapped to some DN in LDAP server, we
wouldn't neccesary be able to find a kerberos data in their LDAP entry.
Instead of searching for Kerberos principal use actual DN we are bound
to because for get_effective_rights LDAP control we only need the DN
itself.
Fixes https://pagure.io/freeipa/issue/6797
"""
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/637/head:pr637
git checkout pr637
From 7201f6dd18014b39d9c96b95ce2f898a55582653 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Wed, 22 Mar 2017 13:00:22 +0200
Subject: [PATCH] ldap2: use LDAP whoami operation to retrieve bind DN for
current connection
For external users which are mapped to some DN in LDAP server, we
wouldn't neccesary be able to find a kerberos data in their LDAP entry.
Instead of searching for Kerberos principal use actual DN we are bound
to because for get_effective_rights LDAP control we only need the DN
itself.
Fixes https://pagure.io/freeipa/issue/6797
---
ipaserver/plugins/ldap2.py | 12
1 file changed, 8 insertions(+), 4 deletions(-)
diff --git a/ipaserver/plugins/ldap2.py b/ipaserver/plugins/ldap2.py
index def1245..b07b708 100644
--- a/ipaserver/plugins/ldap2.py
+++ b/ipaserver/plugins/ldap2.py
@@ -286,12 +286,16 @@ def get_effective_rights(self, dn, attrs_list):
assert isinstance(dn, DN)
-principal = getattr(context, 'principal')
-entry = self.find_entry_by_attr("krbprincipalname", principal,
-"krbPrincipalAux", base_dn=self.api.env.basedn)
+bind_dn = None
+try:
+bind_dn = self.conn.whoami_s()[4:]
+finally:
+if bind_dn is None:
+return None
+
sctrl = [
GetEffectiveRightsControl(
-True, "dn: {0}".format(entry.dn).encode('utf-8'))
+True, "dn: {0}".format(bind_dn).encode('utf-8'))
]
self.conn.set_option(_ldap.OPT_SERVER_CONTROLS, sctrl)
try:
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#621][comment] Add --force-password-reset to user_mod in user.py
URL: https://github.com/freeipa/freeipa/pull/621 Title: #621: Add --force-password-reset to user_mod in user.py abbra commented: """ Ok, let's go with `user-mod` as original request goes, based on the fact that we are not changing the password, we are changing its properties. LGTM. """ See the full comment at https://github.com/freeipa/freeipa/pull/621#issuecomment-287819233 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#621][comment] Add --force-password-reset to user_mod in user.py
URL: https://github.com/freeipa/freeipa/pull/621 Title: #621: Add --force-password-reset to user_mod in user.py abbra commented: """ Hm. `ipa user-mod` has --random and also supports specifying --password, so yes, both interfaces should be provided. """ See the full comment at https://github.com/freeipa/freeipa/pull/621#issuecomment-287772855 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#629][opened] adtrust: make sure that runtime hostname result is consistent with the configuration
URL: https://github.com/freeipa/freeipa/pull/629
Author: abbra
Title: #629: adtrust: make sure that runtime hostname result is consistent
with the configuration
Action: opened
PR body:
"""
FreeIPA's `ipasam` module to Samba uses gethostname() call to identify
own server's host name. This value is then used in multiple places,
including construction of cifs/host.name principal. `ipasam` module
always uses GSSAPI authentication when talking to LDAP, so Kerberos
keys must be available in the /etc/samba/samba.keytab. However, if
the principal was created using non-FQDN name but system reports
FQDN name, `ipasam` will fail to acquire Kerberos credentials.
Same with FQDN principal and non-FQDN hostname.
Also host name and principal name must have the same case.
Report an error when configuring ADTrust instance with inconsistent
runtime hostname and configuration. This prevents errors like this:
[20/21]: starting CIFS services
ipa : CRITICAL CIFS services failed to start
where samba logs have this:
[2017/03/20 06:34:27.385307, 0] ipa_sam.c:4193(bind_callback_cleanup)
kerberos error: code=-1765328203, message=Keytab contains no suitable
keys for cifs/ipatr...@example.com
[2017/03/20 06:34:27.385476, 1]
../source3/lib/smbldap.c:1206(get_cached_ldap_connect)
Connection to LDAP server failed for the 16 try!
Fixes https://pagure.io/freeipa/issue/6786
"""
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/629/head:pr629
git checkout pr629
From b61aa797379709dca6c08b7f9be45fcc1aa102eb Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Mon, 20 Mar 2017 13:23:44 +0200
Subject: [PATCH] adtrust: make sure that runtime hostname result is consistent
with the configuration
FreeIPA's `ipasam` module to Samba uses gethostname() call to identify
own server's host name. This value is then used in multiple places,
including construction of cifs/host.name principal. `ipasam` module
always uses GSSAPI authentication when talking to LDAP, so Kerberos
keys must be available in the /etc/samba/samba.keytab. However, if
the principal was created using non-FQDN name but system reports
FQDN name, `ipasam` will fail to acquire Kerberos credentials.
Same with FQDN principal and non-FQDN hostname.
Also host name and principal name must have the same case.
Report an error when configuring ADTrust instance with inconsistent
runtime hostname and configuration. This prevents errors like this:
[20/21]: starting CIFS services
ipa : CRITICAL CIFS services failed to start
where samba logs have this:
[2017/03/20 06:34:27.385307, 0] ipa_sam.c:4193(bind_callback_cleanup)
kerberos error: code=-1765328203, message=Keytab contains no suitable keys for cifs/ipatr...@example.com
[2017/03/20 06:34:27.385476, 1] ../source3/lib/smbldap.c:1206(get_cached_ldap_connect)
Connection to LDAP server failed for the 16 try!
Fixes https://pagure.io/freeipa/issue/6786
---
ipaserver/install/adtrustinstance.py | 11 +++
1 file changed, 11 insertions(+)
diff --git a/ipaserver/install/adtrustinstance.py b/ipaserver/install/adtrustinstance.py
index 0b18985..1851cc4 100644
--- a/ipaserver/install/adtrustinstance.py
+++ b/ipaserver/install/adtrustinstance.py
@@ -689,6 +689,15 @@ def __enable_compat_tree(self):
except Exception as e:
root_logger.critical("Enabling nsswitch support in slapi-nis failed with error '%s'" % e)
+def __validate_server_hostname(self):
+hostname = socket.gethostname()
+if hostname != self.fqdn:
+raise ValueError("Host reports different name than configured: "\
+ "'%s' versus '%s'. Samba requires to have "\
+ "the same hostname or Kerberos principal "\
+ "'cifs/%s' will not be found in Samba keytab." % \
+ (hostname, self.fqdn, self.fqdn))
+
def __start(self):
try:
self.start()
@@ -809,6 +818,8 @@ def create_instance(self):
self.__create_samba_domain_object)
self.step("creating samba config registry", self.__write_smb_registry)
self.step("writing samba config file", self.__write_smb_conf)
+self.step("validate server hostname",
+ self.__validate_server_hostname)
self.step("adding cifs Kerberos principal",
self.request_service_keytab)
self.step("adding cifs and host Kerberos principals to the adtrust agents group", \
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#621][comment] Add --force-password-reset to user_mod in user.py
URL: https://github.com/freeipa/freeipa/pull/621 Title: #621: Add --force-password-reset to user_mod in user.py abbra commented: """ I would prefer this to be an option in `ipa passwd`, e.g. `ipa passwd --force-reset` which instead of modifying a user password would modify krbPasswordExpiration value. """ See the full comment at https://github.com/freeipa/freeipa/pull/621#issuecomment-287559962 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#617][comment] Allow renaming of sudo rules
URL: https://github.com/freeipa/freeipa/pull/617
Title: #617: Allow renaming of sudo rules
abbra commented:
"""
I don't like it is done on the client side. This will not work for Web UI, for
example.
Additionally, no validation of cn={newname} is here to be a single value RDN.
If we add this as --setattr, we probably want to return meaningful error, not a
general --setattr error.
"""
See the full comment at
https://github.com/freeipa/freeipa/pull/617#issuecomment-287358727
--
Manage your subscription for the Freeipa-devel mailing list:
https://www.redhat.com/mailman/listinfo/freeipa-devel
Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#600][comment] CONFIGURE: Improve detection of xmlrpc_c flags
URL: https://github.com/freeipa/freeipa/pull/600 Title: #600: CONFIGURE: Improve detection of xmlrpc_c flags abbra commented: """ LGTM. Falling back to a standard check is fine. """ See the full comment at https://github.com/freeipa/freeipa/pull/600#issuecomment-286735880 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#573][comment] Provide centralized management of user short name resolution
URL: https://github.com/freeipa/freeipa/pull/573 Title: #573: Provide centralized management of user short name resolution abbra commented: """ Yes, it is expected too. Remember that 'Default Trust View' is a view that applies globally. You have already global setting to apply. """ See the full comment at https://github.com/freeipa/freeipa/pull/573#issuecomment-286456329 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#582][comment] Remove pkinit from ipa-replica-prepare
URL: https://github.com/freeipa/freeipa/pull/582 Title: #582: Remove pkinit from ipa-replica-prepare abbra commented: """ They were in DL0 in `ipa-server-install` for very long time and never worked. We left them there to make sure we can get them back to work sometime later. We did but in new design `ipa-replica-prepare` does not need to use these options, unlike `ipa-server-install`. """ See the full comment at https://github.com/freeipa/freeipa/pull/582#issuecomment-286449785 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#582][comment] Remove pkinit from ipa-replica-prepare
URL: https://github.com/freeipa/freeipa/pull/582 Title: #582: Remove pkinit from ipa-replica-prepare abbra commented: """ LGTM. """ See the full comment at https://github.com/freeipa/freeipa/pull/582#issuecomment-286447734 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#573][comment] Provide centralized management of user short name resolution
URL: https://github.com/freeipa/freeipa/pull/573 Title: #573: Provide centralized management of user short name resolution abbra commented: """ I don't see ACI.txt regenerated. """ See the full comment at https://github.com/freeipa/freeipa/pull/573#issuecomment-286097962 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#570][opened] ipaserver/dcerpc.py: use arcfour_encrypt from samba
URL: https://github.com/freeipa/freeipa/pull/570 Author: abbra Title: #570: ipaserver/dcerpc.py: use arcfour_encrypt from samba Action: opened PR body: """ Samba Python bindings provide samba.arcfour_encrypt(key, data). Instead of implementing own wrapper, use Samba's. In future Samba versions this wrapper will be FIPS 140-2 compatible. Fixes https://pagure.io/freeipa/issue/6697 """ To pull the PR as Git branch: git remote add ghfreeipa https://github.com/freeipa/freeipa git fetch ghfreeipa pull/570/head:pr570 git checkout pr570 From 73610344cab79f32a62b405ffb74d568c98226a3 Mon Sep 17 00:00:00 2001 From: Alexander Bokovoy <aboko...@redhat.com> Date: Fri, 10 Mar 2017 16:47:02 +0200 Subject: [PATCH] ipaserver/dcerpc.py: use arcfour_encrypt from samba Samba Python bindings provide samba.arcfour_encrypt(key, data). Instead of implementing own wrapper, use Samba's. In future Samba versions this wrapper will be FIPS 140-2 compatible. Fixes https://pagure.io/freeipa/issue/6697 --- ipaserver/dcerpc.py | 10 +- 1 file changed, 1 insertion(+), 9 deletions(-) diff --git a/ipaserver/dcerpc.py b/ipaserver/dcerpc.py index f00141b..2d9d7e5 100644 --- a/ipaserver/dcerpc.py +++ b/ipaserver/dcerpc.py @@ -44,11 +44,10 @@ from samba.dcerpc import security, lsa, drsblobs, nbt, netlogon from samba.ndr import ndr_pack, ndr_print from samba import net +from samba import arcfour_encrypt import samba # pylint: enable=import-error -from cryptography.hazmat.primitives.ciphers import Cipher, algorithms -from cryptography.hazmat.backends import default_backend import ldap as _ldap from ipapython import ipaldap from dns import resolver, rdatatype @@ -168,13 +167,6 @@ def assess_dcerpc_exception(num=None, message=None): return errors.RemoteRetrieveError(reason=reason) -def arcfour_encrypt(key, data): -algorithm = algorithms.ARC4(key) -cipher = Cipher(algorithm, mode=None, backend=default_backend()) -encryptor = cipher.encryptor() -return encryptor.update(data) - - class ExtendedDNControl(LDAPControl): # This class attempts to implement LDAP control that would work # with both python-ldap 2.4.x and 2.3.x, thus there is mix of properties -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#564][comment] Reconfigure Kerberos library config as the last step of KDC install
URL: https://github.com/freeipa/freeipa/pull/564 Title: #564: Reconfigure Kerberos library config as the last step of KDC install abbra commented: """ @simo5 KDC starts just fine with missing certs. It disables PKINIT if certs aren't reachable. However, if KDC is not running at all, certmonger cannot complete the cert request at all. """ See the full comment at https://github.com/freeipa/freeipa/pull/564#issuecomment-285426600 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#564][comment] Reconfigure Kerberos library config as the last step of KDC install
URL: https://github.com/freeipa/freeipa/pull/564 Title: #564: Reconfigure Kerberos library config as the last step of KDC install abbra commented: """ LGTM. """ See the full comment at https://github.com/freeipa/freeipa/pull/564#issuecomment-285418391 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#535][comment] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535 Title: #535: add whoami command abbra commented: """ Done. I've also updated the design page to reflect the changes. """ See the full comment at https://github.com/freeipa/freeipa/pull/535#issuecomment-285340468 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#535][synchronized] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535
Author: abbra
Title: #535: add whoami command
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/535/head:pr535
git checkout pr535
From f368e07c6f0fe9fdb8a10602aa6196d7ada9eee7 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Thu, 2 Mar 2017 18:03:05 +0200
Subject: [PATCH] add whoami command
Whoami command allows to query details about currently
authenticated identity. The command returns following information:
* object class name
* function to call to get actual details about the object
* arguments to pass to the function
There are five types of objects that could bind to IPA using their
credentials. `ipa whoami` call expects one of the following:
* users
* staged users
* hosts
* Kerberos services
* ID user override from the default trust view
The latter category of objects is automatically mapped by SASL GSSAPI
mapping rule in 389-ds for users from trusted Active Directory forests.
The command is expected to be used by Web UI to define proper view for
the authenticated identity. It is not visible in the command line
interface is `ipa` command.
Below is an example of how communication looks like for a host
principal:
# kinit -k
# ipa console
(Custom IPA interactive Python console)
>>> api.Command.whoami()
{u'command': u'host_show/1', u'object': u'host', u'arguments': (u'ipa.example.com',)}
>>>
Fixes https://pagure.io/freeipa/issue/6643
---
API.txt | 7 +++
VERSION.m4 | 4 +-
ipaserver/plugins/idviews.py | 5 ++
ipaserver/plugins/whoami.py | 136 +++
4 files changed, 150 insertions(+), 2 deletions(-)
create mode 100644 ipaserver/plugins/whoami.py
diff --git a/API.txt b/API.txt
index ace3101..90cda74 100644
--- a/API.txt
+++ b/API.txt
@@ -6451,6 +6451,12 @@ option: Str('version?')
output: Entry('result')
output: Output('summary', type=[, ])
output: PrimaryKey('value')
+command: whoami/1
+args: 0,1,3
+option: Str('version?')
+output: Output('arguments', type=[])
+output: Output('command', type=[])
+output: Output('object', type=[])
default: aci/1
default: aci_add/1
default: aci_del/1
@@ -7017,6 +7023,7 @@ default: vaultcontainer_add_owner/1
default: vaultcontainer_del/1
default: vaultcontainer_remove_owner/1
default: vaultcontainer_show/1
+default: whoami/1
capability: messages 2.52
capability: optional_uid_params 2.54
capability: permissions2 2.69
diff --git a/VERSION.m4 b/VERSION.m4
index 8c93277..f943566 100644
--- a/VERSION.m4
+++ b/VERSION.m4
@@ -73,8 +73,8 @@ define(IPA_DATA_VERSION, 2010061412)
# #
define(IPA_API_VERSION_MAJOR, 2)
-define(IPA_API_VERSION_MINOR, 219)
-# Last change: Support for Certificate Identity Mapping
+define(IPA_API_VERSION_MINOR, 220)
+# Last change: Add whoami command
diff --git a/ipaserver/plugins/idviews.py b/ipaserver/plugins/idviews.py
index 3ee2be4..b38a4ad 100644
--- a/ipaserver/plugins/idviews.py
+++ b/ipaserver/plugins/idviews.py
@@ -818,6 +818,11 @@ class idoverrideuser(baseidoverride):
label_singular = _('User ID override')
rdn_is_primary_key = True
+# ID user overrides are bindable because we map SASL GSSAPI
+# authentication of trusted users to ID user overrides in the
+# default trust view.
+bindable = True
+
permission_filter_objectclasses = ['ipaUserOverride']
managed_permissions = {
'System: Read User ID Overrides': {
diff --git a/ipaserver/plugins/whoami.py b/ipaserver/plugins/whoami.py
new file mode 100644
index 000..0ec6bb8
--- /dev/null
+++ b/ipaserver/plugins/whoami.py
@@ -0,0 +1,136 @@
+#
+# Copyright (C) 2017 FreeIPA Contributors see COPYING for license
+#
+
+import six
+from ipalib import api, Command, errors, output, Str
+from ipalib import _
+from ipapython.dn import DN
+from ipalib.plugable import Registry
+from .idviews import DEFAULT_TRUST_VIEW_NAME
+
+if six.PY3:
+unicode = str
+
+__doc__ = _("""
+Return information about currently authenticated identity
+
+Who am I command returns information on how to get
+more details about the identity authenticated for this
+request. The information includes:
+
+ * type of object
+ * command to retrieve details of the object
+ * arguments and options to pass to the command
+
+The information is returned as a dictionary. Examples below use
+'key: value' output for illustrative purposes.
+
+EXAMPLES:
+
+ Look up as IPA user:
+ kinit admin
+ ipa console
+ >> api.Command.whoami()
+ --
+ object: user
+ command: user_show/1
+ arguments: admin
+ --
[Freeipa-devel] [freeipa PR#535][comment] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535 Title: #535: add whoami command abbra commented: """ Updated. """ See the full comment at https://github.com/freeipa/freeipa/pull/535#issuecomment-285310604 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#535][synchronized] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535
Author: abbra
Title: #535: add whoami command
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/535/head:pr535
git checkout pr535
From 8813bd25f19656d73342f339d0bc6cab9d00b179 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Thu, 2 Mar 2017 18:03:05 +0200
Subject: [PATCH] add whoami command
Whoami command allows to query details about currently
authenticated identity. The command returns following information:
* object class name
* function to call to get actual details about the object
* arguments to pass to the function
There are five types of objects that could bind to IPA using their
credentials. `ipa whoami` call expects one of the following:
* users
* staged users
* hosts
* Kerberos services
* ID user override from the default trust view
The latter category of objects is automatically mapped by SASL GSSAPI
mapping rule in 389-ds for users from trusted Active Directory forests.
The command is expected to be used by Web UI to define proper view for
the authenticated identity. It is not visible in the command line
interface is `ipa` command.
Below is an example of how communication looks like for a host
principal:
# kinit -k
# ipa console
(Custom IPA interactive Python console)
>>> api.Command.whoami()
{u'command': u'host_show/1', u'object': u'host', u'arguments': (u'ipa.example.com',)}
>>>
Fixes https://pagure.io/freeipa/issue/6643
---
API.txt | 7 +++
VERSION.m4 | 4 +-
ipaserver/plugins/idviews.py | 5 ++
ipaserver/plugins/whoami.py | 141 +++
4 files changed, 155 insertions(+), 2 deletions(-)
create mode 100644 ipaserver/plugins/whoami.py
diff --git a/API.txt b/API.txt
index ace3101..90cda74 100644
--- a/API.txt
+++ b/API.txt
@@ -6451,6 +6451,12 @@ option: Str('version?')
output: Entry('result')
output: Output('summary', type=[, ])
output: PrimaryKey('value')
+command: whoami/1
+args: 0,1,3
+option: Str('version?')
+output: Output('arguments', type=[])
+output: Output('command', type=[])
+output: Output('object', type=[])
default: aci/1
default: aci_add/1
default: aci_del/1
@@ -7017,6 +7023,7 @@ default: vaultcontainer_add_owner/1
default: vaultcontainer_del/1
default: vaultcontainer_remove_owner/1
default: vaultcontainer_show/1
+default: whoami/1
capability: messages 2.52
capability: optional_uid_params 2.54
capability: permissions2 2.69
diff --git a/VERSION.m4 b/VERSION.m4
index 8c93277..f943566 100644
--- a/VERSION.m4
+++ b/VERSION.m4
@@ -73,8 +73,8 @@ define(IPA_DATA_VERSION, 2010061412)
# #
define(IPA_API_VERSION_MAJOR, 2)
-define(IPA_API_VERSION_MINOR, 219)
-# Last change: Support for Certificate Identity Mapping
+define(IPA_API_VERSION_MINOR, 220)
+# Last change: Add whoami command
diff --git a/ipaserver/plugins/idviews.py b/ipaserver/plugins/idviews.py
index 3ee2be4..b38a4ad 100644
--- a/ipaserver/plugins/idviews.py
+++ b/ipaserver/plugins/idviews.py
@@ -818,6 +818,11 @@ class idoverrideuser(baseidoverride):
label_singular = _('User ID override')
rdn_is_primary_key = True
+# ID user overrides are bindable because we map SASL GSSAPI
+# authentication of trusted users to ID user overrides in the
+# default trust view.
+bindable = True
+
permission_filter_objectclasses = ['ipaUserOverride']
managed_permissions = {
'System: Read User ID Overrides': {
diff --git a/ipaserver/plugins/whoami.py b/ipaserver/plugins/whoami.py
new file mode 100644
index 000..1bfc94c
--- /dev/null
+++ b/ipaserver/plugins/whoami.py
@@ -0,0 +1,141 @@
+#
+# Copyright (C) 2017 FreeIPA Contributors see COPYING for license
+#
+
+import six
+from ipalib import api, Command, errors, output, Str
+from ipalib import _
+from ipapython.dn import DN
+from ipalib.plugable import Registry
+from .idviews import DEFAULT_TRUST_VIEW_NAME
+
+if six.PY3:
+unicode = str
+
+__doc__ = _("""
+Return information about currently authenticated identity
+
+Who am I command returns information on how to get
+more details about the identity authenticated for this
+request. The information includes:
+
+ * type of object
+ * command to retrieve details of the object
+ * arguments and options to pass to the command
+
+The information is returned as a dictionary. Examples below use
+'key: value' output for illustrative purposes.
+
+EXAMPLES:
+
+ Look up as IPA user:
+ kinit admin
+ ipa console
+ >> api.Command.whoami()
+ --
+ object: user
+ command: user_show/1
+ arguments: admin
+ --
[Freeipa-devel] [freeipa PR#535][synchronized] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535
Author: abbra
Title: #535: add whoami command
Action: synchronized
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/535/head:pr535
git checkout pr535
From 4a8a7f88e7dfd4f18d24ce5455e64193667cb168 Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Thu, 2 Mar 2017 18:03:05 +0200
Subject: [PATCH] add whoami command
Whoami command allows to query details about currently
authenticated identity. The command returns following information:
* object class name
* function to call to get actual details about the object
* arguments to pass to the function
* options to pass to the function
There are five types of objects that could bind to IPA using their
credentials. `ipa whoami` call expects one of the following:
* users
* staged users
* hosts
* Kerberos services
* ID user override from the default trust view
The latter category of objects is automatically mapped by SASL GSSAPI
mapping rule in 389-ds for users from trusted Active Directory forests.
The command is expected to be used by Web UI to define proper view for
the authenticated identity. It is not visible in the command line
interface is `ipa` command.
Below is an example of how communication looks like for a host
principal:
# kinit -k
# ipa console
(Custom IPA interactive Python console)
>>> api.Command.whoami()
{u'details': u'host_show/1', u'object': u'host', u'arguments': (u'ipa.example.com',), u'options': ()}
>>>
Fixes https://pagure.io/freeipa/issue/6643
---
API.txt | 8 +++
VERSION.m4 | 4 +-
ipaserver/plugins/idviews.py | 5 ++
ipaserver/plugins/whoami.py | 150 +++
4 files changed, 165 insertions(+), 2 deletions(-)
create mode 100644 ipaserver/plugins/whoami.py
diff --git a/API.txt b/API.txt
index ace3101..731b032 100644
--- a/API.txt
+++ b/API.txt
@@ -6451,6 +6451,13 @@ option: Str('version?')
output: Entry('result')
output: Output('summary', type=[, ])
output: PrimaryKey('value')
+command: whoami/1
+args: 0,1,4
+option: Str('version?')
+output: Output('arguments', type=[])
+output: Output('details', type=[])
+output: Output('object', type=[])
+output: Output('options', type=[])
default: aci/1
default: aci_add/1
default: aci_del/1
@@ -7017,6 +7024,7 @@ default: vaultcontainer_add_owner/1
default: vaultcontainer_del/1
default: vaultcontainer_remove_owner/1
default: vaultcontainer_show/1
+default: whoami/1
capability: messages 2.52
capability: optional_uid_params 2.54
capability: permissions2 2.69
diff --git a/VERSION.m4 b/VERSION.m4
index 8c93277..f943566 100644
--- a/VERSION.m4
+++ b/VERSION.m4
@@ -73,8 +73,8 @@ define(IPA_DATA_VERSION, 2010061412)
# #
define(IPA_API_VERSION_MAJOR, 2)
-define(IPA_API_VERSION_MINOR, 219)
-# Last change: Support for Certificate Identity Mapping
+define(IPA_API_VERSION_MINOR, 220)
+# Last change: Add whoami command
diff --git a/ipaserver/plugins/idviews.py b/ipaserver/plugins/idviews.py
index 3ee2be4..b38a4ad 100644
--- a/ipaserver/plugins/idviews.py
+++ b/ipaserver/plugins/idviews.py
@@ -818,6 +818,11 @@ class idoverrideuser(baseidoverride):
label_singular = _('User ID override')
rdn_is_primary_key = True
+# ID user overrides are bindable because we map SASL GSSAPI
+# authentication of trusted users to ID user overrides in the
+# default trust view.
+bindable = True
+
permission_filter_objectclasses = ['ipaUserOverride']
managed_permissions = {
'System: Read User ID Overrides': {
diff --git a/ipaserver/plugins/whoami.py b/ipaserver/plugins/whoami.py
new file mode 100644
index 000..e793cba
--- /dev/null
+++ b/ipaserver/plugins/whoami.py
@@ -0,0 +1,150 @@
+#
+# Copyright (C) 2017 FreeIPA Contributors see COPYING for license
+#
+
+import six
+from ipalib import api, Command, errors, output, Str
+from ipalib import _
+from ipapython.dn import DN
+from ipalib.plugable import Registry
+from .idviews import DEFAULT_TRUST_VIEW_NAME
+
+if six.PY3:
+unicode = str
+
+__doc__ = _("""
+Return a description of currently authenticated identity
+
+Who am I command returns information on who to get
+more details about the identity authenticated for this
+request. The information includes:
+
+ * type of object
+ * command to retrieve details of the object
+ * arguments and options to pass to the command
+
+The information is returned as a dictionary. Examples below use
+'key: value' output for illustrative purposes.
+
+EXAMPLES:
+
+ Look up as IPA user:
+ kinit admin
+ ipa console
+ >> api.Command.whoami()
+ --
+ object
[Freeipa-devel] [freeipa PR#535][comment] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535 Title: #535: add whoami command abbra commented: """ We can disable it for CLI, that's not a problem. """ See the full comment at https://github.com/freeipa/freeipa/pull/535#issuecomment-285085254 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#420][comment] Allow login to WebUI using Kerberos aliases/enterprise principals
URL: https://github.com/freeipa/freeipa/pull/420 Title: #420: Allow login to WebUI using Kerberos aliases/enterprise principals abbra commented: """ Thanks. LGTM and works for me with IPA user, IPA host principal, and AD user. The latter cannot yet actually use Web UI but that is a separate PR. """ See the full comment at https://github.com/freeipa/freeipa/pull/420#issuecomment-285058056 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#420][+ack] Allow login to WebUI using Kerberos aliases/enterprise principals
URL: https://github.com/freeipa/freeipa/pull/420 Title: #420: Allow login to WebUI using Kerberos aliases/enterprise principals Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#547][comment] Use GSS-SPNEGO if connecting locally
URL: https://github.com/freeipa/freeipa/pull/547 Title: #547: Use GSS-SPNEGO if connecting locally abbra commented: """ LGTM but I think we should also update Requires: in the spec file to use cyrus-sasl-2.1.26-29.fc26 or later. """ See the full comment at https://github.com/freeipa/freeipa/pull/547#issuecomment-284736912 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#545][comment] install_check: require IPv6 stack to be enabled
URL: https://github.com/freeipa/freeipa/pull/545 Title: #545: install_check: require IPv6 stack to be enabled abbra commented: """ how the /proc check going to play with containers? """ See the full comment at https://github.com/freeipa/freeipa/pull/545#issuecomment-284738343 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#444][comment] Allow nsaccountlock to be searched in user-find commands
URL: https://github.com/freeipa/freeipa/pull/444 Title: #444: Allow nsaccountlock to be searched in user-find commands abbra commented: """ You are correct in the fact that the search filter need to be modified to allow matching entries without nsAccountLock attribute set. """ See the full comment at https://github.com/freeipa/freeipa/pull/444#issuecomment-284327327 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#444][comment] Allow nsaccountlock to be searched in user-find commands
URL: https://github.com/freeipa/freeipa/pull/444 Title: #444: Allow nsaccountlock to be searched in user-find commands abbra commented: """ The nsaccountlock *is* virtual attribute in 389-ds: attributeTypes: ( 2.16.840.1.113730.3.1.610 NAME 'nsAccountLock' DESC 'Operational attribute for Account Inactivation' SYNTAX 1.3.6.1.4.1.1466.115.121.1.15 USAGE directoryOperation X-ORIGIN 'Netscape Directory Server' ) Notice `USAGE directoryOperation` in the attribute definition. It is treated as a virtual one everywhere in the code but nothing sets it. It is supposed to be set via nsRole and CoS template. See ns-activate.pl/ns-inactivate.pl/ns-accountstatus.pl in 389-ds for external manipulation of it. """ See the full comment at https://github.com/freeipa/freeipa/pull/444#issuecomment-284320588 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#444][comment] Allow nsaccountlock to be searched in user-find commands
URL: https://github.com/freeipa/freeipa/pull/444 Title: #444: Allow nsaccountlock to be searched in user-find commands abbra commented: """ Yes, you can add nsaccountlock attribute retrieval in the `pre_callback` and process it in the `post_callback`. nsaccountlock is an operational attribute so it needs to be requested explicitly. """ See the full comment at https://github.com/freeipa/freeipa/pull/444#issuecomment-283723205 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#535][comment] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535 Title: #535: add whoami command abbra commented: """ Design page: http://www.freeipa.org/page/V4/Who_Am_I_Command """ See the full comment at https://github.com/freeipa/freeipa/pull/535#issuecomment-283716554 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#535][opened] add whoami command
URL: https://github.com/freeipa/freeipa/pull/535
Author: abbra
Title: #535: add whoami command
Action: opened
PR body:
"""
`ipa whoami` command allows to query details about currently
authenticated identity. The command returns following information:
* object class name
* function to call to get actual details about the object
* arguments to pass to the function
* options to pass to the function
There are five types of objects that could bind to IPA using their
credentials. `ipa whoami` call expects one of the following:
* users
* staged users
* hosts
* Kerberos services
* ID user override from the default trust view
The latter category of objects is automatically mapped by SASL GSSAPI
mapping rule in 389-ds for users from trusted Active Directory forests.
The command is expected to be used by Web UI to define proper view for
the authenticated identity.
Below is an example of how communication looks like for an Active
Directory user which has ID override in 'Default Trust View'.
$ ipa -vv whoami
ipa: INFO: trying https://ipa.example.com/ipa/session/json
ipa: INFO: Forwarding 'whoami/1' to json server
'https://ipa.example.com/ipa/session/json'
ipa: INFO: Request: {
"id": 0,
"method": "whoami/1",
"params": [
[],
{
"version": "2.220"
}
]
}
ipa: INFO: Response: {
"error": null,
"id": 0,
"principal": "Administrator@AD.DOMAIN",
"result": {
"arguments": [
"default trust view",
"administrator@ad.domain"
],
"details": "idoverrideuser_show/1",
"object": "idoverrideuser",
"options": []
},
"version": ""
}
Fixes https://pagure.io/freeipa/issue/6643
"""
To pull the PR as Git branch:
git remote add ghfreeipa https://github.com/freeipa/freeipa
git fetch ghfreeipa pull/535/head:pr535
git checkout pr535
From f400b8021a7af27e9d377d3b28fff2ace4eadffc Mon Sep 17 00:00:00 2001
From: Alexander Bokovoy <aboko...@redhat.com>
Date: Thu, 2 Mar 2017 18:03:05 +0200
Subject: [PATCH] add whoami command
`ipa whoami` command allows to query details about currently
authenticated identity. The command returns following information:
* object class name
* function to call to get actual details about the object
* arguments to pass to the function
* options to pass to the function
There are five types of objects that could bind to IPA using their
credentials. `ipa whoami` call expects one of the following:
* users
* staged users
* hosts
* Kerberos services
* ID user override from the default trust view
The latter category of objects is automatically mapped by SASL GSSAPI
mapping rule in 389-ds for users from trusted Active Directory forests.
The command is expected to be used by Web UI to define proper view for
the authenticated identity.
Below is an example of how communication looks like for an Active
Directory user which has ID override in 'Default Trust View'.
$ ipa -vv whoami
ipa: INFO: trying https://ipa.example.com/ipa/session/json
ipa: INFO: Forwarding 'whoami/1' to json server 'https://ipa.example.com/ipa/session/json'
ipa: INFO: Request: {
"id": 0,
"method": "whoami/1",
"params": [
[],
{
"version": "2.220"
}
]
}
ipa: INFO: Response: {
"error": null,
"id": 0,
"principal": "Administrator@AD.DOMAIN",
"result": {
"arguments": [
"default trust view",
"administrator@ad.domain"
],
"details": "idoverrideuser_show/1",
"object": "idoverrideuser",
"options": []
},
"version": ""
}
Fixes https://pagure.io/freeipa/issue/6643
---
API.txt | 8 +++
VERSION.m4 | 4 +-
ipaclient/plugins/whoami.py | 20 ++
ipaserver/plugins/idviews.py | 5 ++
ipaserver/plugins/whoami.py | 141 +++
5 files changed, 176 insertions(+), 2 deletions(-)
create mode 100644 ipaclient/plugins/whoami.py
create mode 100644 ipaserver/plugins/whoami.py
diff --git a/API.txt b/API.txt
index a8f8ff1..16ee0ac 100644
--- a/API.txt
+++ b/API.txt
@@ -6441,6 +6441,13 @@ option: Str('version?')
output: Entry('result')
output: Output('summary', type=[, ])
output: PrimaryKey('value')
+command
[Freeipa-devel] [freeipa PR#526][comment] server install: do not attempt to issue PKINIT cert in CA-less
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: do not attempt to issue PKINIT cert in CA-less abbra commented: """ ACK for the patch. However, I'm not claiming that CA does not need to be trusted. What I'm saying is that for Anonymous PKINIT's use in privilege separation code we can issue certs using local CA because we can trust local CA on IPA masters. They would be all different local CAs, of course, but this was thought to be a stop-gap until admins can replace local certificates with the proper ones some time after upgrade. Privilege separation code now supports several ways to kinit and falls back to a wrapping with HTTP/ipa.master credentials in case anonymous PKINIT is not available. """ See the full comment at https://github.com/freeipa/freeipa/pull/526#issuecomment-283389431 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#526][+ack] server install: do not attempt to issue PKINIT cert in CA-less
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: do not attempt to issue PKINIT cert in CA-less Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#526][comment] server install: properly handle PKINIT-related options
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: properly handle PKINIT-related options abbra commented: """ This PR does not handle upgrade case which is what Local CA considers. We don't need other systems trust the certificate and we don't need to synchronize anything because KDC cert in upgrade case is issued automatically and is used by privilege separation code on the same machine. """ See the full comment at https://github.com/freeipa/freeipa/pull/526#issuecomment-283335425 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#526][comment] server install: properly handle PKINIT-related options
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: properly handle PKINIT-related options abbra commented: """ No, you are wrong. Certmonger has own local self-signed CA in all installs: # getcert list-cas CA 'local': is-default: no ca-type: EXTERNAL helper-location: /usr/libexec/certmonger/local-submit This is what can and should be used for self-signed case for PKINIT. """ See the full comment at https://github.com/freeipa/freeipa/pull/526#issuecomment-283327044 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#526][comment] server install: properly handle PKINIT-related options
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: properly handle PKINIT-related options abbra commented: """ This was, perhaps, missed in the original commit, though. The idea was that in CA-less mode we change request to use Local CA. """ See the full comment at https://github.com/freeipa/freeipa/pull/526#issuecomment-283327401 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#526][comment] server install: properly handle PKINIT-related options
URL: https://github.com/freeipa/freeipa/pull/526 Title: #526: server install: properly handle PKINIT-related options abbra commented: """ An idea behind the original solution was to always produce PKINIT certificate by certmonger in case of CA-less install to be able to have anonymous PKINIT supported. PKINIT cert should have specific attributes and in many cases they aren't issued by external CAs. However, the certificate is not really needed to be connected to existing CAs. Admins can re-issue PKINIT cert afterwards but at least we can get anonymous PKINIT to wrap 2FA with. So this pull request actually breaks CA-less deployment. """ See the full comment at https://github.com/freeipa/freeipa/pull/526#issuecomment-283322805 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#444][comment] Allow nsaccountlock to be searched in user-find commands
URL: https://github.com/freeipa/freeipa/pull/444 Title: #444: Allow nsaccountlock to be searched in user-find commands abbra commented: """ nsaccountlock is an operational attribute, not a normal one. I don't like it being created all the time. You have to request it explicitly if you want to show status of users, not invent a mechanism to always add it. """ See the full comment at https://github.com/freeipa/freeipa/pull/444#issuecomment-283260530 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#516][comment] IdM Server: list all Employees with matching Smart Card
URL: https://github.com/freeipa/freeipa/pull/516 Title: #516: IdM Server: list all Employees with matching Smart Card abbra commented: """ One thing I don't like is that SELinux policy requirements aren't mentioned. To allow ipaapi user to talk to SSSD dbus interface, you have to have a policy that allows this. """ See the full comment at https://github.com/freeipa/freeipa/pull/516#issuecomment-283003886 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#479][comment] Merge AD trust installer into composite ones
URL: https://github.com/freeipa/freeipa/pull/479 Title: #479: Merge AD trust installer into composite ones abbra commented: """ Unless you specified --add-sids to ipa-adtrust-install (or `add_sids=True` in ADTrustInstance.setup() call), no task would be run. 'Activating sidgen task' only adds configuration to allow the task to be run. """ See the full comment at https://github.com/freeipa/freeipa/pull/479#issuecomment-282777294 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#508][comment] Fix ipa.service unit re. gssproxy
URL: https://github.com/freeipa/freeipa/pull/508 Title: #508: Fix ipa.service unit re. gssproxy abbra commented: """ Good point. I think we shouldn't restart ourselves as we anyway are listening on all interfaces with 0.0.0.0. """ See the full comment at https://github.com/freeipa/freeipa/pull/508#issuecomment-282757529 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#479][comment] Merge AD trust installer into composite ones
URL: https://github.com/freeipa/freeipa/pull/479 Title: #479: Merge AD trust installer into composite ones abbra commented: """ If you can differentiate how the installer is being run, then for composite installer always run add_sids. """ See the full comment at https://github.com/freeipa/freeipa/pull/479#issuecomment-282739260 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#508][+ack] Fix ipa.service unit re. gssproxy
URL: https://github.com/freeipa/freeipa/pull/508 Title: #508: Fix ipa.service unit re. gssproxy Label: +ack -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#508][comment] Fix ipa.service unit re. gssproxy
URL: https://github.com/freeipa/freeipa/pull/508 Title: #508: Fix ipa.service unit re. gssproxy abbra commented: """ LGTM. Thank you finding and fixing this issue. """ See the full comment at https://github.com/freeipa/freeipa/pull/508#issuecomment-282467859 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
[Freeipa-devel] [freeipa PR#468][comment] Remove non-sensical kdestroy on https stop
URL: https://github.com/freeipa/freeipa/pull/468 Title: #468: Remove non-sensical kdestroy on https stop abbra commented: """ @tiran we do use PrivateTmp already. This is not about PrivateTmp, though, because we don't store credentials caches in a private tmp. """ See the full comment at https://github.com/freeipa/freeipa/pull/468#issuecomment-280618508 -- Manage your subscription for the Freeipa-devel mailing list: https://www.redhat.com/mailman/listinfo/freeipa-devel Contribute to FreeIPA: http://www.freeipa.org/page/Contribute/Code
