[
https://issues.apache.org/jira/browse/NIFI-4005?page=com.atlassian.jira.plugin.system.issuetabpanels:comment-tabpanel&focusedCommentId=16292182#comment-16292182
]
ASF GitHub Bot commented on NIFI-4005:
--------------------------------------
Github user ijokarumawak commented on a diff in the pull request:
https://github.com/apache/nifi/pull/1886#discussion_r157142645
--- Diff:
nifi-nar-bundles/nifi-azure-bundle/nifi-azure-processors/src/main/java/org/apache/nifi/processors/azure/storage/utils/Azure.java
---
@@ -0,0 +1,124 @@
+/*
+ * Licensed to the Apache Software Foundation (ASF) under one or more
+ * contributor license agreements. See the NOTICE file distributed with
+ * this work for additional information regarding copyright ownership.
+ * The ASF licenses this file to You under the Apache License, Version 2.0
+ * (the "License"); you may not use this file except in compliance with
+ * the License. You may obtain a copy of the License at
+ *
+ * http://www.apache.org/licenses/LICENSE-2.0
+ *
+ * Unless required by applicable law or agreed to in writing, software
+ * distributed under the License is distributed on an "AS IS" BASIS,
+ * WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
+ * See the License for the specific language governing permissions and
+ * limitations under the License.
+ */
+package org.apache.nifi.processors.azure.storage.utils;
+
+import com.microsoft.azure.storage.CloudStorageAccount;
+import com.microsoft.azure.storage.StorageCredentials;
+import com.microsoft.azure.storage.StorageCredentialsSharedAccessSignature;
+import com.microsoft.azure.storage.blob.CloudBlobClient;
+import org.apache.commons.lang3.StringUtils;
+import org.apache.nifi.components.PropertyDescriptor;
+import org.apache.nifi.components.ValidationContext;
+import org.apache.nifi.components.ValidationResult;
+import org.apache.nifi.logging.ComponentLog;
+import org.apache.nifi.processor.ProcessContext;
+import org.apache.nifi.processor.util.StandardValidators;
+
+import java.net.URI;
+import java.net.URISyntaxException;
+import java.security.InvalidKeyException;
+import java.util.ArrayList;
+import java.util.Collection;
+import java.util.List;
+
+public final class Azure {
+ public static final String BLOCK = "Block";
+ public static final String PAGE = "Page";
+
+ public static final PropertyDescriptor ACCOUNT_KEY = new
PropertyDescriptor.Builder().name("storage-account-key").displayName("Storage
Account Key")
+ .description("The storage account key. This is an admin-like
password providing access to every container in this account. It is recommended
" +
+ "one uses Shared Access Signature (SAS) token instead
for fine-grained control with policies. " +
+ "There are certain risks in allowing the account key
to be stored as a flowfile" +
+ "attribute. While it does provide for a more flexible
flow by allowing the account key to " +
+ "be fetched dynamically from a flow file attribute,
care must be taken to restrict access to " +
+ "the event provenance data (e.g. by strictly
controlling the policies governing provenance for this Processor). " +
+ "In addition, the provenance repositories may be put
on encrypted disk partitions.")
+
.addValidator(StandardValidators.NON_EMPTY_VALIDATOR).expressionLanguageSupported(true).required(false).sensitive(true).build();
+
+ public static final PropertyDescriptor ACCOUNT_NAME = new
PropertyDescriptor.Builder().name("storage-account-name").displayName("Storage
Account Name")
+ .description("The storage account name. There are certain
risks in allowing the account name to be stored as a flowfile" +
+ "attribute. While it does provide for a more flexible
flow by allowing the account name to " +
+ "be fetched dynamically from a flow file attribute,
care must be taken to restrict access to " +
+ "the event provenance data (e.g. by strictly
controlling the policies governing provenance for this Processor). " +
+ "In addition, the provenance repositories may be put
on encrypted disk partitions.")
+
.addValidator(StandardValidators.NON_EMPTY_VALIDATOR).expressionLanguageSupported(true).required(true).sensitive(true).build();
+
+ public static final PropertyDescriptor CONTAINER = new
PropertyDescriptor.Builder().name("container-name").displayName("Container
Name")
+ .description("Name of the Azure storage
container").addValidator(StandardValidators.NON_EMPTY_VALIDATOR).expressionLanguageSupported(true).required(true).build();
+
+ public static final PropertyDescriptor PROP_SAS_TOKEN = new
PropertyDescriptor.Builder()
+ .name("SAS String")
--- End diff --
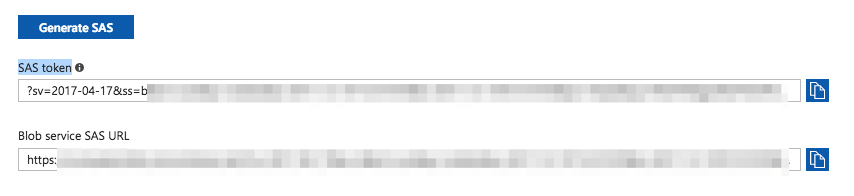
Please use name and displayName as other properties do. "SAS Token" would
be better go along with Azure terminology. Especially when I copied value from
Azure Web console, I could be more confident where should I copy the value from
if it's labeled as "SAS Token".
> Add support for Azure Shared Access Signature (SAS) Tokens
> ----------------------------------------------------------
>
> Key: NIFI-4005
> URL: https://issues.apache.org/jira/browse/NIFI-4005
> Project: Apache NiFi
> Issue Type: Improvement
> Components: Extensions
> Affects Versions: 1.2.0
> Reporter: Andrew Grande
> Priority: Minor
>
> Azure's account name and key are treated as admin, 'root' access credentials.
> If one has those, every container under this account is fully accessible. An
> MSFT-recommended approach is to use SAS policies, which provide for a fine
> grained permission and object control, as well as defined expiration.
> I already have working code, filing this ticket to formally track and submit
> PR against next.
--
This message was sent by Atlassian JIRA
(v6.4.14#64029)
